Tor markets and cryptomarkets facilitate seamless transactions, making darknet sites a preferred choice for discreet online shopping. Darknet markets have become a cornerstone for secure and reliable drug trade in 2025, offering users a platform that prioritizes anonymity, efficiency, and quality control. These platforms leverage advanced encryption technologies and decentralized systems to ensure that transactions remain private and secure. The use of onion addresses and Tor networks further enhances user privacy, making it nearly impossible for third parties to trace activities. mark it means it has been verified as a scam service and it should be avoided. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge.|However, due to copyright infringement, Sci-Hub is considered illegal and banned in many countries. Keybase also offers extremely user-friendly secure chat and file-sharing services through its app. Keybase is an exciting identity service that aims to make it easy for you to link the presence of your online identities together in a cryptographic way. You can upload your PGP key or have the site create one for you, and use it to cryptographically link your Twitter profile, Github account, or Bitcoin address together. Based in Switzerland, ProtonMail is an encrypted email service that is very popular with cryptocurrency enthusiasts.|Don’t forget to include links to mirrors.txt and pgp.txt of the service you want to list, so that I can verify them before listing. However, any illegal activities conducted on the dark web, such as purchasing illicit goods or engaging in criminal behavior, are still punishable by law. For most people and use cases, using only a VPN will offer sufficient privacy with much faster speeds than Tor alone.|The combination of improved security and user-centric design makes modern cryptomarkets more accessible than ever. The Tor network routes connections through a series of volunteer-operated servers, obscuring the user’s IP address. Each server only knows the previous and next hop, ensuring no single point can reveal the entire path. This decentralized approach prevents third parties from linking buyers or sellers to their transactions. A Canadian market established in 2021, WTN offers over 9,000 products, including narcotics, fake goods, and digital services. It operates in both French and English and has built a reputation for ease-of-use.|This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime. ProPublica is a popular online publication that won five Pulitzers in 2016. It aims to expose abuses of power and betrayal of public trust through investigative journalism.}
What Is The Best Dark Web Search Engine?
Monero’s blockchain obfuscation complements PGP by hiding transaction details. Unlike Bitcoin, Monero conceals sender, receiver, and amount, adding another layer of privacy. Combined with PGP, these measures create a secure environment for transactions.
- You can access onion sites only through the Tor browser or special network configurations.
- The browser uses onion routing technology to route the internet traffic through multiple relay nodes that provide layered encryption.
- These platforms, accessible via darknet links and onion addresses, offer anonymity and convenience for users.
- That said, most experts agree that at least some nodes on the Tor network have been compromised by intelligence agencies like the CIA and the NSA.
This adds extra protection since opening Tor itself encrypts your traffic. A virtual private network (VPN) is a good way to mask Tor activities. It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there.

Encrypted Communication Tools
It is also used by whistle-blowers, journalists, and other individuals who are not involved in illegal activity but need to protect their communications and identities. Through the dark web, users in places of high censorship can also access information and news. To make its journalism more accessible to readers around the world, the New York Times launched its onion service in 2017. While you don’t need to log in to access any of the dark web links listed here, you can’t find them with a search engine like Google. The only way to access the dark web is by using the correct browser and knowing the URLs of the pages you want to visit.
Navigating Darknet Market Links Safely

The dark web is part of the internet that is not indexed by standard search engines like Google, Yahoo, and Bing. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it. Gabe The Russian DNM Hydra topped the list led by White House cypher market and others. This sector appears as a vector for laundering funds of illicit origin. The transactions were reportedly worth a total of 4,650 bitcoin and 12,800 monero – two cryptocurrencies – for an equivalent of more than $A221 million.

Can You Be Traced On Tor?
Our advanced escrow system requires multiple signatures to release funds, preventing exit scams and ensuring fair transactions for both buyers and sellers. Access verified Ares onion links, comprehensive security guides, and real-time market status updates. Darknet markets — also known as cryptomarkets — provide a largely anonymous platform for trading in a range of illicit goods and services.
Communication Security And PGP Encryption
Monitoring these markets involves understanding their operational structures, examining transaction patterns, and tracking the flow of illegal commodities. Law enforcement agencies often collaborate with cybersecurity entities to track and shut down these sites, many of which consistently rotate their onion addresses to evade detection. Awareness of the prevalent darknet market onion addresses can provide valuable insights into the evolving landscape of illegal online trade. The darknet drug market has expanded significantly in 2025, driven by advancements in privacy technologies and the rise of new cryptomarkets. Platforms like Nexus Market and Abacus Market dominate due to their streamlined interfaces, robust encryption, and reliable vendor systems. These markets prioritize user safety through features like PGP-verified communications and multisig escrow, reducing fraud risks.
Why Using Trusted Directories And Security Tools Is Important
Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace. Therefore, you must run an IP leak test to ensure that the VPN is working completely fine and is not risking your digital security. DarkOde Reborn is a great darknet market where you can find anything you want. The website has a great design and a clean and organized interface that is easy to use. The homepage includes options like browsing products, searching, mixer, and coin exchange. You need to register first to purchase products from this marketplace.
Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every visitor is a criminal, but this is where most cybercrimes begin. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together.
The 10 Biggest Dark Web Markets In 2025 – Updated List & Security Insights
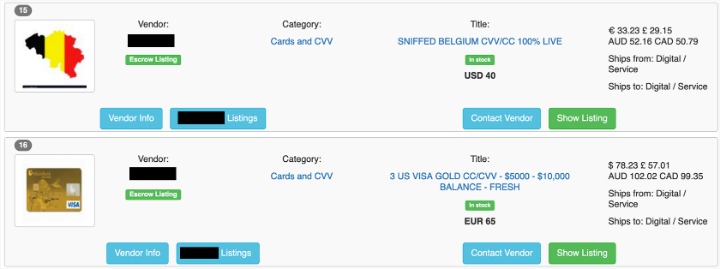
Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. Others are looking for stolen data, hacking services, or even banned books and political content. For sellers, it’s often about making money while staying off the radar.
Up To 10GB Of Saily Mobile Data For Free
Use it to search the normal internet from the privacy of your Tor Browser. Torch is one of the oldest and most popular onion search engines on the dark web, serving over 80,000 requests per day. Torch is funded primarily through advertising—purchased in BTC, of course—which is why you’ll find the front page blanketed with old-school banner ads of dubious origins. Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts. Your real information could be exposed at these nodes, allowing third parties to intercept your dark web activity. That’s why we recommend connecting to VPN before accessing Tor—VPN encryption protects your data, and changing your IP adds an extra layer of privacy to protect you.
That ensures trust and safety for every user exploring Ares darknet products. Advanced tracking tools help you monitor price trends, vendor reliability, and product availability across the Ares darknet marketplace. With its low 5% vendor fee, secure transactions, and verified sellers, it’s an ideal choice for buyers looking for a trusted marketplace. Darknet markets prioritize financial anonymity, making Bitcoin and Monero the dominant payment methods in 2025. Monero, however, has gained prominence for its built-in privacy features, automatically encrypting sender, receiver, and amount details through ring signatures and stealth addresses. Newer cryptomarkets adopt onion routing through Tor, masking IP addresses effectively.
The Tor Browser, a modified version of Firefox, is a common gateway to these services. It routes traffic through multiple layers of encryption, masking users’ identities and locations. For additional security, many users employ virtual private networks (VPNs) to encrypt their internet traffic. These features collectively make the darknet a reliable environment for drug trade in 2025, offering users a seamless and secure experience.
It has a bidding feature, with new batches of stolen data being frequently added. Active for a decade since 2014, it is a widely used credit card shop used to source stolen credit card information such as dumps, CVVs, Wholesale Accounts. If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address.