However, the website has some security risks, and users experience glitches. The marketplace has a pleasant, user-friendly interface built from the ground up. Its interface makes it easy to identify clone websites and ensures that users always use the authentic site. During our tests for the research, we were able to register with a bogus email and a random username.
Impact On Businesses And Cybersecurity
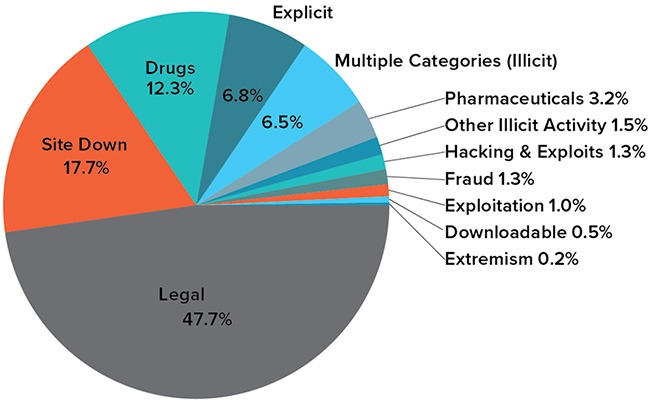
In the first arc of the anime series Lupin the 3rd Part V, Lupin III steals digital currency from the “Marco Polo” darknet market. Whilst a great many products are sold, drugs dominate the numbers of listings, with the drugs including cannabis, MDMA, modafinil,108109110 LSD, cocaine, and designer drugs. One of the central76 discussion forums was Reddit’s /r/DarkNetMarkets/,777879 which has been the subject of legal investigation, as well as the Tor-based discussion forum, The Hub. Using TAILS is yet another security measure that protects your online identity on the dark web. It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer.

Is It Illegal To Access The Dark Web?

This article reveals the top 10 dark web markets dominating in 2025, their unique characteristics, and the critical implications for enterprise cybersecurity. Since its inception, the market has catered to criminals looking for high-quality counterfeit items, such as fake IDs, passports, and branded luxury goods. Fresh Tools Market has become a go-to platform for cybercriminals seeking access to malicious software such as keyloggers, Remote Access Trojans (RATs), and ransomware-as-a-service. The Russian Market has been around since 2019 and is one of the more prominent dark web marketplaces. Transactions are conducted through Bitcoin and Monero which provides anonymity for both buyers and sellers.
Dark Web Hackers Pay For Facial Images And Supporting Identity Documents—Users Willingly Participate
Recognizing the ethical and moral dimensions of this issue represents an essential first step toward reducing its prevalence and fostering a more trustworthy, responsible society. Additionally, communities facing rampant document fraud often see declining public trust in institutions, businesses, and even interpersonal relationships. When citizens perceive that fraud is widespread or tolerated, social cohesion weakens, damaging overall community resilience and stability. Due to the cross-border nature of cybercrimes, international cooperation is essential.
Malware / Exploit Kit Services:
This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet. Since the dark web can be accessed through the Tor browser, use a VPN with the Tor browser to ensure increased protection. A VPN hides the fact that you’re using Tor, which is blocked in some countries and always raises doubts because of its criminal reputation. Commenting on the findings, Andrew Newell, Chief Scientific Officer at iProov warned against selling personally identifiable information to anyone.
As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. So I have found a seller for a fake UK drivers license which they claim is registered with the DVLA. And has 19 positive feedback but none actually mention if it is actually registered on the database or not. Ultimately, addressing fake document usage necessitates more than law enforcement—it requires broader societal reflection and moral education emphasizing integrity, accountability, and the importance of shared societal values.
- Accessing any darknet marketplace is dangerous because it is known to be a hub for illegal trade.
- We recommend using NordVPN as it offers top-notch security features, including dark web threat protection.
- Palo Alto Networks Next-Generation security platform provides a holistic solution to protect the digital way of life by safely enabling applications and preventing known and unknown threats across the network, cloud and endpoints.
- Launched in 2020, Cypher Marketplace sells fraudulent documents, stolen credit cards, fake IDs, and malware.
- The platform’s activity has increased significantly over the past year, indicating its growing influence and market share in the underground economy.
- The Identity Theft Research Center reported that 1,291 breaches had occurred till October 2021, compared to a total of 1,108 in 2020.
Launched in 2020, Cypher Marketplace sells fraudulent documents, stolen credit cards, fake IDs, and malware. Its emphasis on user anonymity and document forgery makes it a core tool for identity fraud. Creating a brand new financial profile is a popular service offered by many dark web marketplaces — anyone can renew their financial status — with brand new bank accounts, new credit cards, a new credit score, and even new PayPal accounts. There are also financial related services that can be purchased on the dark web, like fixing bad credit ratings or providing a counterfeit cash-injection in exchange for Bitcoin.
Fake Ids?
After the Biker DLC, players can now purchase buildings for illegal drugs and counterfeit products manufacture, and distribute them through a darknet website called “The Open Road” where law enforcement cannot be notified of the player’s trade. At KELA, we help you identify and mitigate risks by providing actionable intelligence from the darknet. Our solutions empower you to monitor illicit darknet marketplaces and track emerging threats, ensuring you can take proactive measures to protect your organization and reputation.
The market frequently makes headlines for releasing massive troves of stolen data, often as a way to advertise its services. The market is known for its extensive product listings and reputation system that helps buyers evaluate the reliability of vendors. The market emphasizes anonymity and security, conducting transactions exclusively through cryptocurrencies like Bitcoin and Monero.
How To Protect Your Personal Data Online
- Hydra, a Russian-language Dark Web marketplace, operated for years before its 2022 takedown by German authorities, demonstrating the adaptability of these underground economies.
- Image of counterfeit ID card and underground economy tools Artificially generated image.
- Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring.
- Once the purchase order has been completed, the Bitcoins are released to the Seller (Vendor).
- So far in 2021, the number of data breaches have already surpassed last year’s total.
- While it hosts legitimate uses, such as protecting privacy in oppressive regimes, it is also infamous for facilitating illegal trade in drugs, weapons, counterfeit documents, and stolen corporate data.
Apart from the dark web markets that are operating online today, some raided platforms influenced many markets. Security researchers have been monitoring forums within the cybercriminal underworld to investigate the leading markets operating in 2024. These markets were inspired by the Silk Road, the first high-profile darknet marketplace launched in 2011 by Ross Ulbricht. His idealistic vision of an open marketplace ran on libertarian philosophies and Bitcoin. By consistently applying these comprehensive preventative measures, individuals, businesses, and governments can significantly reduce vulnerabilities to fake document fraud, safeguarding their identities and assets from exploitation.

But no matter how polished or professional these sites seem, the risk of getting scammed — or tracked — is always high. Most buyers and sellers use the Tor network, which hides IP addresses and locations. Doing so makes it harder for authorities to identify who’s behind a purchase or a listing. Vendors often build up reputations through ratings and reviews, just like sellers on mainstream platforms. To reduce scams, many markets also use escrow systems, where the site holds the buyer’s payment until they confirm the item has been delivered.
This guide shows businesses how digital identities are compromised, traded on the black market, and misused, and importantly, how to protect your organization and customers. A woman in New Brunswick had her account hijacked; what started as a simple Facebook login ended with her friends being scammed out of thousands. The scammer used her digital identity by sending fake messages to her contacts, collecting payments fraudulently, and then disappearing without a trace. Your account must be older than 4 days, and have more than 20 post and 10 comment karma to contribute.
It enhances buyer transparency by importing vendor feedback with PGP proof. Torzon offers a premium account option for additional benefits and is valued at approximately $15 million, accepting payments in Bitcoin (BTC) and Monero (XMR). WeTheNorth is a Canadian market established in 2021 that also serves international users. It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process. Financial institutions employ strict KYC regulations designed to prevent fraud and money laundering.