Prices are, however, expected to fall in case of a new cryptocurrency upturn, as this would lead to increased interest and hype from the general public. The table above shows how much the prices of processing account details have fallen in the last year due to the high supply. It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder. If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic.
How To Find Dark Web Websites
- Declan Harrington pled guilty to doing SIM-swapping attacks, and of course, Shane Sonderman from Episode 106 was arrested for SIM-swapping, and currently he’s spending five years in prison.
- However, data is required for understanding, monitoring, and improving the network.
- Cybercriminals can use your personal information to take out loans in your name, claim your tax returns, or open new credit cards.
- Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents.
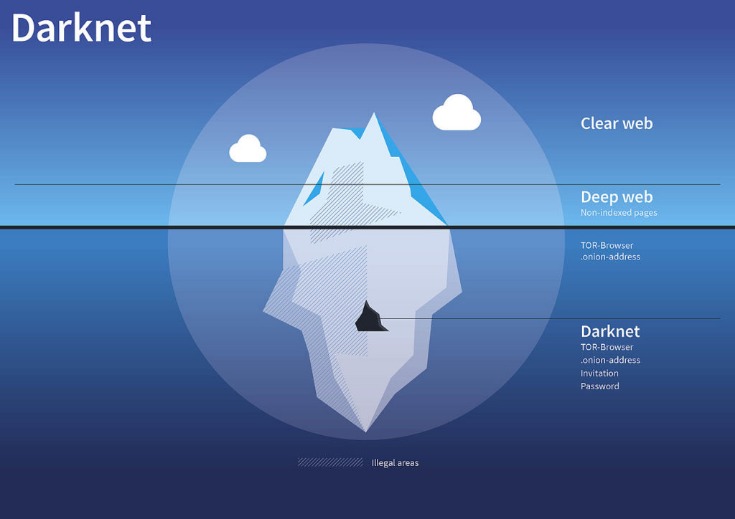
As a result, the recommended browser for accessing the dark web is the Tor (The Onion Router) browser. However, please note this article is for research and educational purposes only. The dark net is full of notorious hackers, scammers, malware, and other viruses.
- Although it offers leaks from many different countries, the site has a dedicated lookup and leak section for Canadian profiles, making it extremely easy to use for buyers interested in Canadian leaks.
- You only need to upload your PGP key or let the platform create one.
- Other methods of collecting financial data included the use of malware and skimming.
- This allows them to access funds illegally and engage in activities such as money laundering and embezzlement.
- Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals.
- These kids are blowing it as fast as they get it, and almost all of them have gambling addictions, where they’ll put some money in an online casino and spin the wheel and try to hit it even bigger.
Unfortunately, keeping your SSN off of the dark web may be out of your control. Cybercriminals are more likely to target big organizations than specific individuals, and if those organizations’ defenses fail, there’s not much you can do as a client. However, you can still take measures to minimize the impact of your SSN or other sensitive information being compromised. In the first arc of the anime series Lupin the 3rd Part V, Lupin III steals digital currency from the “Marco Polo” darknet market. The months and years after Silk Road’s closure were marked by a greatly increased number of shorter-lived markets as well as semi-regular law enforcement takedowns, hacks, scams and voluntary closures.
Elliptic Analysis: A Troubled Criminal Enterprise Struggling To Survive
In many cases, the SSNs offered for sale on the Dark Web are either fake or belong to unsuspecting victims. Using such information can lead to severe consequences, such as financial liabilities, damaged credit history, and legal complications. The Dark Web is a complex and ever-evolving ecosystem due to its hidden nature and the constant efforts to maintain anonymity. It is a realm where trust, reputation systems, and encrypted communication play a crucial role in facilitating transactions. Understanding its workings and the risks involved is essential for anyone exploring this hidden corner of the internet.
However, there’s no guarantee that all the links on this site are working. Some may lead to malicious sites, downloading malware on your device. Onion sites are far safer to use as they are hidden deep within the deep web. Also, since users can only access them using the Tor browser (with its high-end encryption), users can be rest assured their identities and locations remain hidden. Use a password manager to generate and store strong, unique passwords for all your accounts.
This means your activities cannot be traced or your browser history exposed. These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes. As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web.
Cyble Titan Endpoint Security
Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web.
Frequently Asked Questions (FAQs) About Dark Web Marketplaces

We ensured that the dark web sites we chose had reviews and feedback from real users on other forums; this way, we can be sure of the site’s reliability and legitimacy. Ahmia is a safe alternative search engine for users who prefer the dark web. It also provides insights, helpful statistics, and updates regarding the Tor network. Phishing was one of the most common methods identified by Equifax as a tool for collecting financial information on the dark web. This is a methodology that involves an attacker gathering someone’s card details by asking them to provide information as part of an unsolicited email.
Breaking: The Cheapest VPN In History Is About To Disappear (Final Hours)
Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities.
Dark.fail is an easy-to-use .onion platform equipped with a status checker that tracks website uptime. The site offers access to PGP-verified URLs and runs free of JavaScript or tracking. This platform’s library of websites currently totals 50, which may not sound impressive until you consider that all the links are active and popular.
Payment Processing Services
According to the IBM Cost of a Data Breach Report 2023 report, it took organizations over 200 days to identify a breach and then another 73 days to contain it. For example, ProPublica—a renowned investigative journalism non-profit— uses the dark web to communicate with whistleblowers and ensure readers can access content without facing retaliation. That is important for those who may fear persecution for their actions or live in areas where access to information is regulated. If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API.
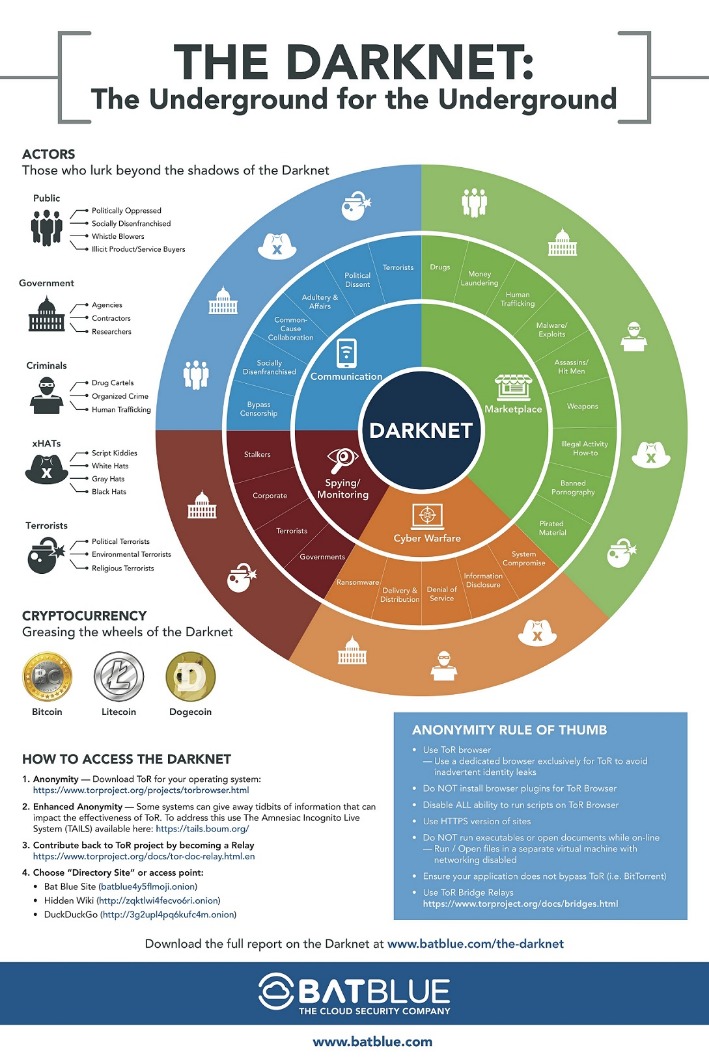
How To Access The Dark Web

Cybercriminals who purchased this information could use it to conduct phishing attacks and blackmail scam campaigns, as well as to create accounts on social media and financial services under assumed identities. Dark web monitoring platforms, such as Lunar, provide an automated solution to safeguard personal identifiable information (PII) and credit card details. These platforms continuously scour the deep and dark web, looking for any traces of your sensitive information. By setting up alerts, businesses can receive notifications whenever their PII or credit card information appears in suspicious contexts. This proactive monitoring enables businesses to track and investigate potential threats in real-time, helping to prevent fraud before it can impact their operations.
Subscribe To Our Blog For More News And Updates!
According to a report from Secure World, spending on the dark net hauled in record revenue during 2020, which may have had something to do with the impact of the pandemic on people’s finances, and state of mind. The research shows 2020 was the first year for dark net activity to go over $1.5 billion. The Abacus Market links to the new dark web marketplace sections and took over much of the vacuum left by the AlphaBay takedown. If you ever decide to explore the dark web, protecting your identity is crucial.
Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation. Patterns recommended to avoid include hiring hitmen like Dread Pirate Roberts, and sharing handles for software questions on sites like Stack Exchange. One of the central76 discussion forums was Reddit’s /r/DarkNetMarkets/,777879 which has been the subject of legal investigation, as well as the Tor-based discussion forum, The Hub.
Dark Web Websites: How To Access Them Safely
Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. You can choose the best darknet (.onion) website that suits you and start surfing. For safer browsing, it is highly recommended to also use a VPN and antivirus software.