They usually accept cryptocurrencies, such as Bitcoin, which keeps transactions secret. There are no visible ads or trackers, and the design is often very simple. Your ISP, and possibly the authorities, may decide to start monitoring your activity more closely to look for threats or illegal activity. That’s why we always recommend using a VPN over Tor—even if you feel you have nothing to hide. This just involves turning on your VPN before you open Tor and connect to dark web sites.

These categories include email providers, news sites, privacy, and commercial services. Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation. Patterns recommended to avoid include hiring hitmen like Dread Pirate Roberts, and sharing handles for software questions on sites like Stack Exchange. But anything that’s against the law on the regular web or offline is also illegal on the dark web. This includes buying or selling illicit goods, illegal transactions, and downloading copyrighted material.
While no approach guarantees complete safety, a careful and skeptical mindset serves as one of your most valuable tools on the hidden internet. Law enforcement agencies keep an ear to the ground on the dark web looking for stolen data from recent security breaches that might lead to a trail to the perpetrators. Many mainstream media organizations monitor whistleblower sites looking for news.
Bitcoin Boosts Privacy In Darknet Drug Trade
The extra connection layers can act as a significant burden to your browsing experience if you’re doing something that is bandwidth intensive. As we mentioned above, when you connect to Tor your data first goes through an entry node, which can see your IP address. By connecting to a VPN before using Tor, you mask your real IP address before it reaches this entry node, adding an extra layer of security and anonymity.
E-mail Newsletter
But if you are thinking you can find links to the deepest part of the dark web using this site, it’s not that simple. However, there’s no guarantee that all the links on this site are working. With each random server, your traffic bounces off, and a layer of encryption gets added. These layers upon layers give this network its iconic “onion” name—as the onion itself has layers upon layers.
- Like regular browsers with domain names, the Tor browser also has its own domain designation.
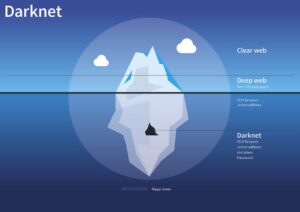
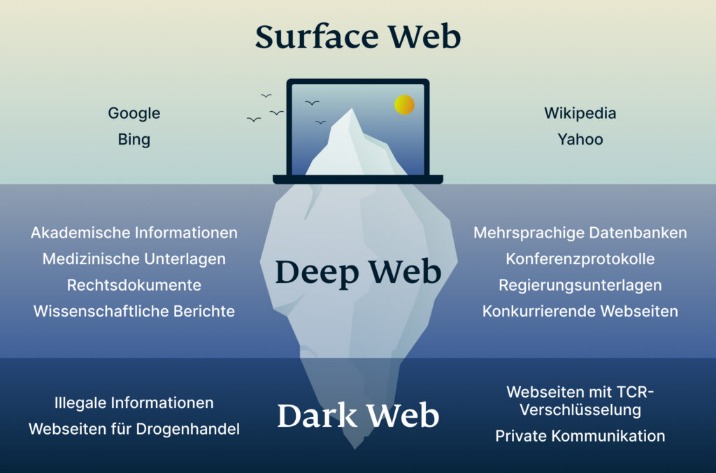
- So, if you want to know how to access the dark web safely, you need to understand that the vast majority of the dark web, or dark net, is only accessible through the Tor browser.
- This adds another, more reliable security layer to all of your online activity.
- The combination of advanced technology, user-centric design, and a commitment to privacy ensures that darknet markets remain a viable option for secure and reliable drug trade in 2025.
- Again, not all the dark web is used for illicit purposes despite its ominous-sounding name.
- Another private cryptocurrency you’ll find being used is Monero, which prides itself on being untraceable.
Why Monero Over Bitcoin?
But as long as you don’t knowingly engage in illicit activity on the dark web, you are completely fine. However, note that Dark.fail monitors site uptime status and cannot tell whether the site is safe. To stay safe and private when visiting any listed sites, ensure you have a VPN and anti-malware installed and enabled. With its nifty “conjoin” feature, users can combine different coins in one transaction, covering the user’s tracks and maintaining their anonymity. The wallet is user-friendly and provides robust security, making it one of the best crypto wallets on the dark web.
The Cyber Express News
DigDeeper offers in-depth analysis of technology and privacy topics rarely covered by mainstream media. The website’s articles focus on digital rights, surveillance, and security research. I found their technical explanations clear and well-researched, though the site updates less frequently than other news platforms. Ever since Silk Road went down, several dark web marketplaces have kept coming and several of them shut down again. To stop the marketplaces is not a walk in the park as it takes immense effort from authorities like the FBI and international law enforcement. The fact that there are no real regulations as well as authorities to monitor transactions, you’re always on your own, and you’re a potential target and victim of a scam or fraud.
Best Free VPNs For The Dark Web In 2025: Secure & Fast
Unlike traditional search engines, it doesn’t track or store personal information, ensuring your searches stay private. It’s a popular choice for users worried about online surveillance and data collection. In addition, Darknetlive has a list of dark web vendors, which is very convenient — it offers detailed information about each vendor, including .onion addresses (in alphabetical order) and FAQs. DuckDuckGo is a search engine available on the Tor network that lets you browse the surface and dark web. Essentially, it’s a search engine like Google or Safari, but unlike other search engines, it doesn’t track your browsing activity or collect user data.

This ongoing innovation ensures that these platforms remain at the forefront of secure and efficient drug trade, offering users a seamless and anonymous shopping experience. The growing popularity of darknet drug markets is driven by their ability to provide a safe and anonymous environment for trade. Users benefit from the convenience of browsing extensive product catalogs, secure communication channels, and reliable delivery systems.
How To Avoid Phishing Scams And Malware Threats
Proton Mail’s dark web version provides end-to-end encrypted email with enhanced privacy protection. The service doesn’t require personal information to create an account and works seamlessly through Tor. I found in my tests that all features work identically to the regular version.
It enhances buyer transparency by importing vendor feedback with PGP proof. Torzon offers a premium account option for additional benefits and is valued at approximately $15 million, accepting payments in Bitcoin (BTC) and Monero (XMR). Always transfer your cryptocurrency to a personal wallet under your control before making purchases on darknet markets. Never send coins directly from an exchange, and avoid storing funds in market-hosted wallets. By controlling your own keys, you significantly reduce the risk of losing access to your money if a market exit scams, gets seized, or simply goes offline. By following safe access methods—like verified onion market lists, secure browsing practices, and strong OPSEC—you greatly reduce these risks.

Hidden Wiki
It has a vast library of over 1.5 billion indexed pages that lets you find whatever you are looking for. However, the threat of clicking on the wrong link always remains, so be cautious while you use it. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. Further market diversification occurred in 2015, as did further developments around escrow and decentralization. ZLibrary hosts free file-sharing access to academic texts, scholarly articles, and general-interest books.
This mechanism holds funds in a secure account until the buyer confirms receipt of the product, reducing the risk of fraud. Additionally, multi-signature transactions are increasingly common, requiring multiple parties to approve a payment, further enhancing trust between users. One of the key factors driving the success of darknet markets is the emphasis on vendor ratings and product diversity. Users can access detailed reviews and ratings for each vendor, ensuring that they engage only with trusted sellers. This system fosters a competitive environment where vendors strive to maintain high standards, resulting in better quality products and services. Additionally, the wide range of available products caters to diverse preferences, making these markets a one-stop solution for users.
Tor And The Onion Browser
Most darknet market administrators are now tightening access controls. Every potential participant’s credentials must be vigorously vetted before they can join. That way, they aim to create secure forums and limit outsiders like law enforcement.
It doesn’t censor out any content, so you’ll have free access to more than 400,000 indexed pages. I like that you can ask the search engine to match all of your search words for exact results, or only some of them for broader search results. Of course, bypassing paywalls is ethically questionable and may be illegal in some jurisdictions. That’s why many people choose to do so anonymously on the dark web, rather than using the clear web version of the site. Some locations block access to the site, so the New York Times began hosting on the dark web to unblock links to their news and make it accessible to everyone around the world.
In addition, mainstream search engines also track your searches and collect personal information. Mega Market is a new yet popular shop on the dark web that reached a skyrocketing reputation after the closure of the Hydra market. It allows you to buy and sell a wide range of products and services with a good user experience. This site supports PGP encryption and two-factor authentication features.