Some P2P enable off-ramping via cash and prepaid vouchers, bypassing AML compliance under claims of mere facilitation....
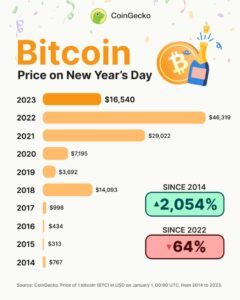
bitcoin
According to Check Point Research, schools and other educational institutions were the most targeted sectors, with attacks...
In contrast, BTMs use blockchain to execute transactions that send the cryptocurrency to the user’s wallet through...
While these types of hacks and sales are ultimately impossible to prevent, individuals can take critical steps...
Once the seller confirms payment, the BTC is released directly to the buyer’s Bisq wallet. Users retain...
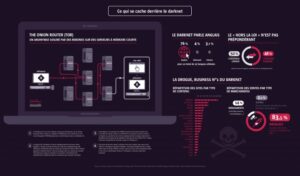
In this guide, we’ll take a deep dive into the Tor market, exploring its history, its culture,...
While it has been used for illegal activities, Bitcoin has also been used for legitimate purposes in...
Cryptocurrencies allow extremist organizations to bypass conventional financial limitations, leveraging pseudonymity to mobilize foreign funds. Terror groups...
It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be...
In addition, the content on the pages don’t need any special or custom configuration to access. Typically,...