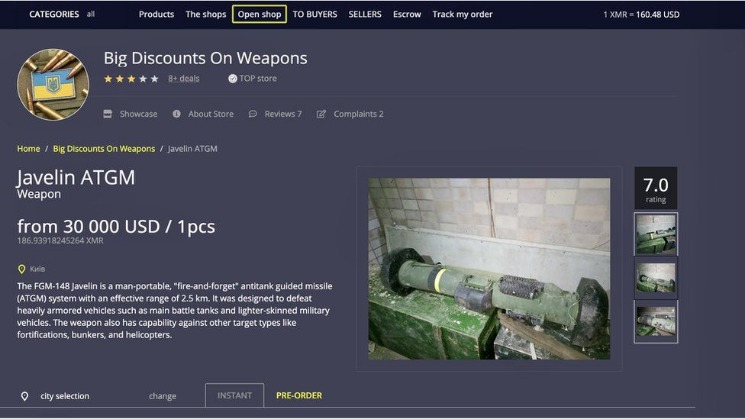
The Reactor graph below shows five purchases made to fraud shops, four of which passed through intermediary addresses. Governments must adapt rapidly, crafting agile legal frameworks that balance innovation with accountability. Private cybersecurity firms must strengthen partnerships with regulators to track illegal transactions and monitor emerging threats. Blockchain analytics tools must evolve to include privacy coins and decentralized systems. The continued growth of dark web markets creates urgent concerns for cybersecurity professionals. Stolen data remains a top-selling commodity, with new breaches appearing almost daily.
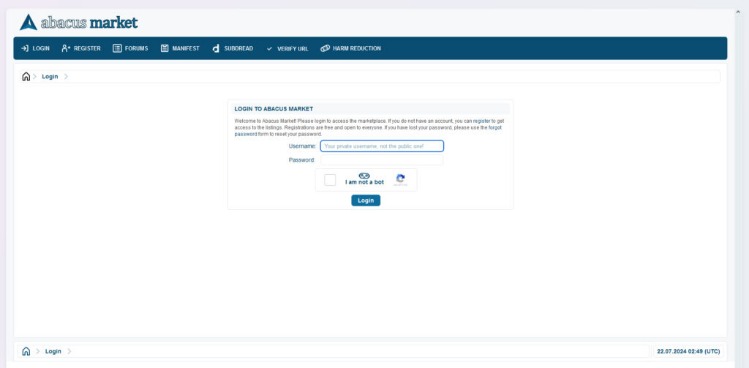
Abacus Market In The Darknet Onion Link URL
It enables the calculation of more precise and distinctive vendor embeddings by incorporating factors such as posting activity, price fluctuations, and changes in product categories. This approach provides a robust foundation for subsequent applications, including vendor identification and the analysis of illicit trading patterns across darknet marketplaces. Unlike Western darknet markets that predominantly rely on vendor bond systems to regulate vendor activity, the Chinese darknet trading market’s subscription-based model substantially lowers barriers to entry. This structure enables vendors to more easily create multiple accounts, circumvent platform sanctions, and sustain illicit operations with relative ease.
🔐JOIN OUR CYBER WORLD CVE News • HackMonitor • UndercodeNews
- How Kaspersky researchers obtained all stages of the Operation Triangulation campaign targeting iPhones and iPads, including zero-day exploits, validators, TriangleDB implant and additional modules.
- Law enforcement and cybersecurity teams must prioritize real-time threat intelligence and zero-trust architectures.
- Because darknet markets are decentralized and operate outside of traditional legal frameworks, there is little recourse for users who are scammed or defrauded.
- Dark web marketplaces are mostly hubs for illicit goods and activities, posing serious risks to users and the wider community.
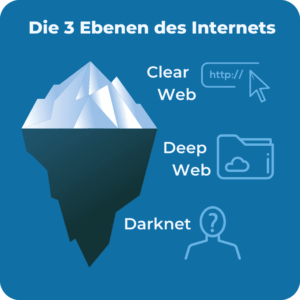
All that one can expect from a deep web marketplace when it comes to anonymity and security. All users on Ares darknet benefit from encrypted transactions, full Monero support, and anonymized routing within the Ares onion system. This article reveals the top 10 dark web markets dominating in 2025, their unique characteristics, and the critical implications for enterprise cybersecurity. Let’s get this straight — not everything on the dark web is illegal or harmful. In fact, some parts of it actually provide a safe space for privacy and freedom, especially where traditional internet access is limited or censored. One of the most common types of illicit goods is stolen login credentials, often collected from data breaches.
How Darknet Links And Onion Addresses Protect Privacy In Drug Trade
- In 2025, the darknet continues to provide a secure and efficient platform for the drug trade, offering users unparalleled privacy and convenience.
- Unlike traditional darknet markets, which are hosted on centralized servers and managed by a single entity, decentralized marketplaces operate on a peer-to-peer (P2P) network.
- In terms of vendor behavior, the change is largely dominated by wholesale vendors.
- This ensures that both buyers and vendors can operate without fear of exposure.
- Security protocols on these platforms are continuously updated to address emerging threats.
Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details. Therefore, for security reasons, disable JavaScript on the Tor browser and enjoy an anonymous browsing experience on the dark net. To register on Abacus Market, you will need to set up an account using a username and password. The platform also requires users to create a PIN for additional security. After passing a CAPTCHA test to avoid bots, you’ll receive a confirmation email to complete the registration process. We provide regularly updated, authenticated Ares URLs to ensure you never fall victim to phishing sites.
Tor markets and darknet sites maintain robust security protocols, ensuring user privacy and transaction integrity. The Darknet marketplace, operating on anonymous communication techniques, has become a central hub for illicit trade, enabling elusive vendors to engage in illegal activities. Identifying and profiling these vendors is critical for effective cyberspace governance and combating cybercrime, financial fraud, and other criminal enterprises. However, the inherent anonymity of the Darknet, along with the use of jargon and coded language, presents significant challenges when relying solely on traditional textual features for vendor identification. In this study, we propose a novel vendor profiling approach that integrates latent behavioral features with textual data, forming the Dark Web Latent Behavior Profiling Framework (DarkBIP-FW).
Usually, buyers and sellers would have trouble connecting and hence justifying large-scale international trafficking. Darknets solve this problem by offering retail quantities of drug types that are traditionally difficult to source, such as MDMA, directly to buyers. Additionally, we may see some of Joker’s Stash’s users migrating to Yale Lodge. Some former Joker’s Stash users have been seen actively inquiring on how to register on Yale Lodge, as they look for new marketplaces to profit from. The number of products posted by sellers is an important behavioral feature indicator. Some sellers tend to post a small number of products across multiple platforms, while others prefer to post multiple times on the same platform.
Exit Scams

The fight against cybercrime is ongoing, complex, and necessitates continuous collaboration and innovation. Exploring the hidden corners of the internet reveals a variety of goods. For greater privacy, Monero is often recommended due to its enhanced features. The key is understanding how each cryptocurrency functions and what level of discretion it can offer.
Top Dark Web Markets In 2025:
With many dark web marketplaces coming and going, finding a safe and reputable platform is more important than ever. In 2025, only a few markets stand out for their security, reliability, and vendor quality. You can find items like digital goods, software, and even collectibles. Some markets have services related to cybersecurity, while others might list more controversial items. The selection depends on the marketplace, and not everything found is legal.
Key Features
Hackers bundle login credentials, credit card details, and identity documents for sale in bulk. Global law enforcement agencies face mounting challenges in tracking and dismantling dark web operations. In 2025, authorities have increased efforts to identify illicit transactions, monitor suspicious wallet activities, and take down infrastructure supporting criminal trade. However, the rapid evolution of these marketplaces continues to outpace many of these initiatives. Vendors and marketplaces have invested in advanced cybersecurity defenses.
Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. In response, darknet market vendors are increasingly shifting their financial activity toward decentralized platforms. While Russian-language markets are well known for serving only Russians, experts say that’s not the dominant darknet market language globally. “English continues to serve as the lingua franca of the underground,” said Gray.
Monitoring Darknet Threat Intelligence With OSINT Tools
Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation. Patterns recommended to avoid include hiring hitmen like Dread Pirate Roberts, and sharing handles for software questions on sites like Stack Exchange. Abacus Market continues to evolve, introducing new features and security enhancements in 2025 to ensure a reliable darknet experience. Stay informed about platform updates, vendor policies, and industry trends.
Microsoft Warns About New Variant Of XCSSET Malware On MacOS
With continuous innovations and emerging contenders, this segment sees rapid changes. More platforms may rise, offering better security, wider selection, or new ways of enhancing user experience. By staying attuned to customer needs and technological advancements, they evolve. You must still be vigilant about your online activities and what you choose to download or view.