
Oh, and don’t ever discuss the actual mechanics of the stealthing methods in a public forum. Okay, you’ve got the bitcoins in your wallet and you’ve encrypted your address with your vendors PGP key. Click “Buy…” then paste your encrypted message into the box and press “Confirm” for your order. You’ll need to make sure you’ve got all the funds in your wallet. So import the vendors key, type out your name and address in full, including country if the source is from abroad. It may seem scary, but I assure you that your postman is more likely to be suspicious that you’re suddenly receiving a lot of packages for John Smith, who only seems to have recently moved in to your place.
- I felt that to have credibility amongst drug consumers this was an essential pre-requisite.
- However, there’s been no formal evaluation of online and street drug sales that can attest to the relative purity and safety of what’s sold in either place—and illegal drugs always come with a safety risk, regardless of where they are bought from.
- So ive been checking out some markets mostly just for fun but also to compare.
- The three nodes separate your IP address from your destination and enable two individuals to communicate without either party, or any middleman, knowing who the other is.
- We evaluated our method on our annotated data set, which yields an accuracy of over 90% for each property extraction, as shown in Table 5.
- TorLinks serves as a backup or secondary directory site to the popular Hidden Wiki.
Torch is one of the oldest and most popular onion search engines on the dark web, serving over 80,000 requests per day. Torch is funded primarily through advertising—purchased in BTC, of course—which is why you’ll find the front page blanketed with old-school banner ads of dubious origins. Onion sites (aka Tor sites) are websites only accessible on the dark web; you can’t view them using a regular browser. Their URLs (aka dark web links) have .onion as the domain, instead of the common surface web domains like .com or .net. They also use their Telegram channels as an online sales channel. In general, ATW BH -which is of USA origin and against China and Russia- hacks documents, personal information, and information that has a privileged background that belongs to the target companies, groups, or countries.

Why Are All The Darknet Markets Down
All their actions and leaks are published on their Twitter accounts and their Telegram group, which everyone can easily access. Withdrawals began failing & admin ceased responding in February 2014; date closure to the forum admin account’s last login. Part of the TorMarket user list was leaked by DPR2 on SR2F; TM also admitted other security issues, but further rumors that TorMarket’s shut down was precipitated by a hack by “Profesorhouse” have not been substantiated. If you browse the dark web using the Tor Browser, your IP address will be hidden from the sites you visit. When you use Tor, your traffic is routed through multiple relays (or servers). The final relay before reaching your destination is the IP address you’ll appear to have.
This move could transform ChatGPT from a subscription-driven platform into a multi-billion-dollar advertising engine. They evolved step by step, shaped by technology, culture, and human behavior. What started as experiments in privacy turned into a global phenomenon — one that continues to spark curiosity, debate, and concern. Whether you see them as cautionary tales or fascinating case studies, they’re proof that the internet, like any society, has both its main streets and its back alleys. Both of these claims correspond with previous research showing that the dark web is perceived to be a safer place to buy and sell drugs. Trade is booming despite disruptions from law enforcement and particularly “exit scams”, in which market admins abruptly close down sites and take all available funds.
Best Onion Sites By Category
And beware—while many explore out of curiosity or for research purposes, it’s important to remember that engaging with these platforms, even as an observer, can lead to serious legal and ethical consequences. When one goes down, two more emerge with new ideas, better technology, and greater difficulty to track. It’s an ever-evolving ecosystem—constantly shifting, reinventing itself, and adapting. To be clear, I don’t nor do I want to sell drugs, personally I don’t see the risk being worth the potential profit. In this way, we collected 7100 promotion posts and 6408 review posts from forum posts in total.
Market Operations
- The way this works is that bitcoins use a blockchain so that you can track where it’s been throughout its existence.
- I have Electrum, but scarecely the foggiest how crypto works.
- Encrypt your address with the vendors key and save it to your clipboard.
- Hence, every word has 2 vectors, each describing the word’s relations with other words in one corpus.
I wanna provide labelled products, good advice and service, like a real business. Not sit in a shitty car park selling $10 bags from a car window all day. This page may contain sensitive or adult content that’s not for everyone. To view it, please log in to confirm your age.By continuing, you also agree that use of this site constitutes acceptance of Reddit’s User Agreement and acknowledgement of our Privacy Policy. A VPN protects your connection against everyone, not just your ISP and the authorities.
Characteristics Of Suppliers
After that, an agent from Homeland Security came in along with a state detective to question me. I played dumb at first because the package had been on my hands for less than 10 seconds. I told them I wasn’t expecting a package and I was simply there to pick up all my mail. Then they played a couple of unconstitutional interrogation tactics on me. They told me they were going to hit my house with a search warrant and I was also going to go to jail that day if I didn’t talk. I was told that I was going to be free to leave that day if I talked (they can’t do this, but this didn’t help my case). The idea of my house getting hit in broad daylight in the neighborhood I’ve lived in for 15 years had me scared to death. The homeland security agent gave me the correct lines…that they were not after me, they wanted the vendor, and they wanted to use my login info on Empire to communicate with my vendor.
Dread’s Origin

The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods. These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar. Fast forward to now, and hidden marketplaces are still around, but the conversation has shifted. Researchers, journalists, and even everyday internet users debate their impact.
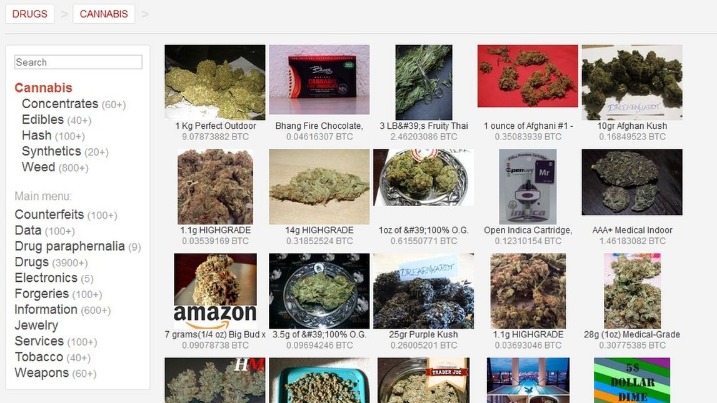
It can be pretty tempermental though and suffers from downtime occasionally. The other most used market is BlackBank but I don’t have any personal experience with this. On the page for each listing, users could pick a predefined quantity of the drug chosen by the vendor, typically measured in grams or number of pills, and proceed to checkout.
No Ask Vendor / Seller
This just involves turning on your VPN before you open Tor and connect to dark web sites. While technically not an onion site, we’re including Sci-Hub (sci-hub.se) as an interesting example of a site you can access via Tor. Sci-Hub gives access to millions of scientific papers, mostly ones from behind paywalls. However, due to copyright infringement, Sci-Hub is considered illegal and banned in many countries. A favorite of journalists and their anonymous sources, SecureDrop makes it easy to share confidential information without revealing your identity. Many news publications, like the ones listed above, have a SecureDrop on their .onion sites.
Note that the escrow mechanism is widely deployed in the anonymous online market because it helps to build trust and resolve disputes between sellers and buyers. When the purchase is made, the opioid trader ships the purchased item to the buyer (step 10). Once the item is received, the buyer finalizes the purchase by notifying the anonymous online marketplace to release the funds held in escrow (step 11) 8,9. After that, an opioid buyer often leaves review comments under the product listing or discusses the purchasing experience in the forum (step 12).
World Market Darknet
He taught me about the general safety of tor, the use of encryption, tumbling crypto, and the increased quality of product when bought from good vendors. The Abacus Market links to the new dark web marketplace sections and took over much of the vacuum left by the AlphaBay takedown. These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information. The second category consists of data stores, which specialize in stolen information. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down.
What People Are Saying

If you are using Tor Browser but still can’t access an onion site, it’s possible that the link has changed (the Tor Project upgraded onion links to become much longer during 2017-’18), or the site simply no longer exists or is temporarily down. You could try to visit a major site like Facebook’s onion site to check if your browser is working at all. This would verify if it’s a browser issue or just an issue with the site.
(Facebook and Instagram took action against 9.3 million pieces of drug-related content last year, while Snapchat says it did so in 241,227 cases in the second half of 2023.) But these companies’ actions are sometimes indiscriminate. The accounts of organizations promoting drug harm reduction and social media personalities who post content about drugs and psychedelics, but who do not sell them, are being caught in the crossfire of efforts to get a grip on the issue. In addition to Empire Market’s more than 18,000 drug listings, another site called Nightmare Market now lists 28,000 drug products, along with the dark web’s usual assortment of stolen credit card numbers, counterfeits, and hacking tools.



