Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace. Therefore, you must run an IP leak test to ensure that the VPN is working completely fine and is not risking your digital security. In 2013, the FBI shut down the Silk Road, but it was later relaunched in 2014 with the new name of Silk Road 2.0, but the German authorities shut it down in the same year. Other than the Silk Road 2.0, similar marketplaces also emerged, but they all went down sooner or later. Tor2door Market is among the largest dark net shops you must visit in 2025 if you’ve decided to visit such sites. On average, the marketplace consists of more than 11,000 items and 1000 vendors.
Which Tools Are Required To Access The Dark Web?
- Back then, the dark web was a niche curiosity for cyberpunks and tech rebels.
- Most likely, the native account on your device has full admin permissions by default.
- For instance, cryptocurrencies like Bitcoin are commonly used for payments because they offer a degree of anonymity.
- In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites.
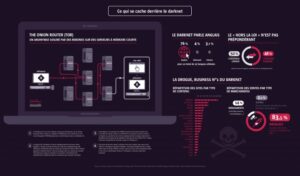
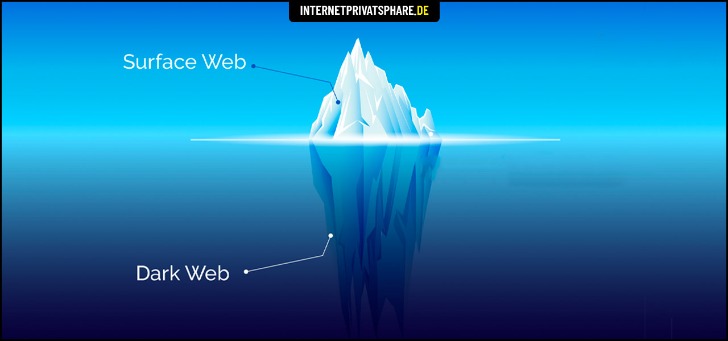
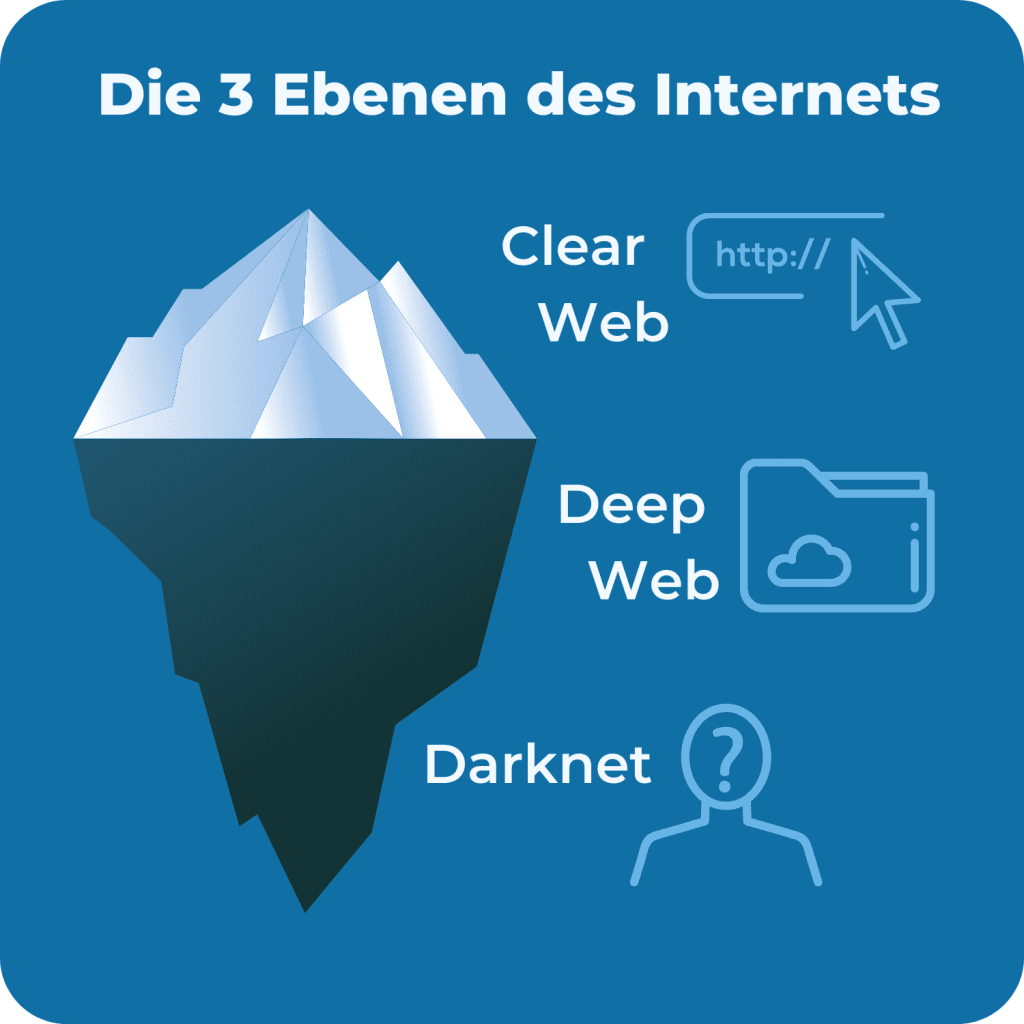
Estimates place the size of the deep web at between 96% and 99% of the internet. Only a tiny portion of the internet is accessible through a standard web browser—generally known as the “clear web”. Surfshark supports unlimited simultaneous connections to protect as many devices as possible. Also, try its services risk-free with the 30-day money-back guarantee. This will help you to remain anonymous and secure at all Tor entry and exit nodes.
Trusted Directories And Forums (stay Away From Hidden Wiki)
Although some other vendors state that they use FedEx and FedEx international to ship overseas. Additionally, credentials are not required to view content on this site, which is uncommon on most DNMs. Therefore, it is a good site to explore if you do not want to create credentials and/or are new to the darknet.
The Silk Road Marketplace
Though Genesis Market domains and servers were seized and antivirus programs have been updated, cybercriminals have already rebuilt illicit services like these. Mega Darknet Market is the dominant drug supply source for drug vendors on other darknet sites, holding a 63.4% share of that market. When looking at darknet drug markets serving Russia-based customers, Kraken Market captured 30.9% of market share, with Blacksprut and Mega Darknet markets closely following. As for drug markets serving Western customers, ASAP Market held a 25.0% share, followed by Mega and Incognito. Western drug flows in particular come from US-domiciled exchanges and trace flows from those to darknet markets.
However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes. As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. Wasabi is one of the most popular cryptocurrency wallets on the dark web. Also, you can set a strong password to protect your message and choose how long it will take to expire.
It sells stolen card data — dumps, CVVs, even wholesale batches — and lets users bid on fresh leaks. Despite multiple takedown efforts by law enforcement and security researchers, Brian’s Club has resurfaced repeatedly and continues to add new stolen credit card data. From drug sales and breached data to scam services and malware, dark web markets are some of the most dangerous corners of the internet. These markets mimic traditional e-commerce websites, but instead of second-hand books or vintage jackets, they traffic in illegal goods and criminal services. Despite consistent results, this study has limitations that may be addressed in future work. First, while the dataset is preprocessed with state-of-the-art methods, there is no ground truth for validation, and this uncertainty propagates to our findings.
Dark Web Tools And Services
This early detection allows organizations to identify and respond to threats quickly, reducing the chances of unauthorized access, financial loss, or damage to brand reputation. A handful of markets were responsible for trafficking most of the data. See how our intelligent, autonomous cybersecurity platform harnesses the power of data and AI to protect your organization now and into the future. Learn effective strategies for conducting threat hunting in your organization. In repressive regimes, darknets play a vital role in enabling free speech and access to uncensored information. Tools like Tor are used to bypass government-imposed firewalls and surveillance, ensuring open communication.
Share This Article
Another dark net marketplace that has grabbed a lot of attention is the Hydra market. The entire website is in Russian, but the vendors are present worldwide. It accepts payments through Bitcoin and the Escrow system and ensures that your identity remains anonymous during your purchases. The marketplace has a pleasant, user-friendly interface built from the ground up. Its interface makes it easy to identify clone websites and ensures that users always use the authentic site. During our tests for the research, we were able to register with a bogus email and a random username.

Common Scams On Dark Web Marketplaces
In the U2U network, an edge connects nodes that are not necessarily users of the same market. Previous studies have shown that, although the number of users and transactions is larger in markets, the trading volume in the U2U network is larger than that of markets13. We use data of DWM transactions on the Bitcoin blockchain pre-processed by Chainalysis Inc. Although other coins are used, such as Monero recently, Bitcoin is still the mostly used in the ecosystem, being supported by more than 93% of markets7,9. The pre-processing relies on established state-of-the-art heuristics to cluster addresses into entities, such as cospending, intelligence-base, and behavioral clustering39,40,41,42. The resulting data set includes for each transaction the source and destination entities, the time, and the value of the transaction.

From identity theft to law enforcement surveillance, the dangers are real — and often underestimated. As law enforcement agencies’ tactics improve, some markets respond by introducing more security features, like mandatory encryption or invite-only access. But no matter how polished or professional these sites seem, the risk of getting scammed — or tracked — is always high. We classify all entities either as sellers or buyers as a function of time.
Zoom Vs Microsoft Teams Statistics 2025: Who Leads In Users, Features & Growth
While Tor anonymizes your connection, a VPN adds an extra layer of security by hiding Tor usage from your internet provider and reducing traceability. Store funds in wallets you control, avoid market-hosted wallets, double-check payment addresses, and consider using privacy-focused coins or mixing services to reduce traceability. Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions. Since 2020, 2easy has sold massive stealer logs with sensitive data like passwords, bank cards, and initial access credentials.
For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy. For operations security he suggests avoiding storing conversation logs, varying writing styles, avoiding mobile phone-based tracking and leaking false personal details to further obfuscate one’s identity. Whilst a great many products are sold, drugs dominate the numbers of listings, with the drugs including cannabis, MDMA, modafinil,108109110 LSD, cocaine, and designer drugs.
Tor2door Market
Radar Rundown Free firewall software allow privacy ethusuiasts to secure their network and block mal… The unique part is that the platform offers free samples of stolen information, often to attract more customers. Also, set up two-factor authentication (2FA) to add an extra layer of protection in case someone manages to figure out your password. Moreover, if you must use public Wi-Fi, ensure that you use a VPN to mask your browsing activity and keep yourself secure. In this era, it takes one wrong click and all your sensitive data ends up in the wrong hands. Therefore, you need to take your privacy seriously and start by using strong and unique passwords for every online account you open.