One genuine exception is a site called Keybase, which helps you securely share files and chat online. It uses public key cryptography to ensure the chats remain anonymous to everyone except the participants. Founded around 1999 by activists in Seattle, it has since grown to over six million users worldwide.

Using a reliable VPN with Tor provides a way to improve security when accessing dark web links. The VPN encrypts your traffic before it enters the Tor network, preventing your ISP from seeing that you’re using Tor. This double encryption also protects against compromised Tor entry nodes that could potentially monitor your activity. The dark web hosts both valuable resources and significant risks. While some .onion sites provide essential services like secure communication and censorship-free journalism, others spread malware or run scams.

Which Is Better — Tor Over VPN Or VPN Over Tor?
- I recommend bookmarking verified links rather than relying on search results.
- Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though).
- This means that the JavaScript will be disabled by default on every website and some symbols and images will not be displayed.
- When you access this site, do so with extra protection, even if you are technically anonymous when you use the Tor browser.
ZeroBin encrypts and decrypts text in the browser, so their servers have no way of knowing what’s happening on the browser side. One of the most straightforward ways to access to dark web safely is via Tor, so we’ve kept that in mind when compiling our list. The last item on our dark web websites list is Google Feud or rather its evil twin.
Popular Dark Web Search Engines: An Overview Of Ahmia, DuckDuckGo onion, Torch, And Not Evil
Facebook’s onion portal is an essential communication tool for people living under oppressive regimes, despite the social media giant’s controversial reputation when it comes to privacy. So, you took my course on how to get on the dark web and want to explore your newfound superpower? To access the dark web, you will need the Tor browser, which provides the necessary anonymity and security.
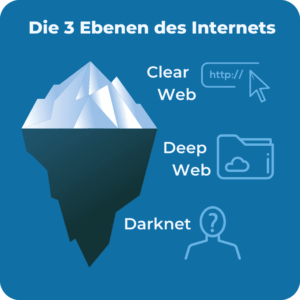
Vorm Web Search Engine
Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc. Other sites explicitly block search engines from identifying them. It works by sending internet traffic through volunteer-operated nodes all over the world. This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites.
One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is online. After more than a year of no updates, the site admin shut it down, reasoning that he couldn’t keep the list of onion links up-to-date. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links.
Data Sheets
Many prominent media sources and journalists maintain a presence on this website location to securely accept documents from anonymous senders. These include big names, such as Al Jazeera, CBC, Forbes, Huffington Post, The New York Times, and many more. Unlike Ahmia and Haystak, however, DuckDuckGo doesn’t search .onion sites. Use it to search the normal internet from the privacy of your Tor Browser.
What Kind Of Content Is On The Dark Web?
It’s something built into the password management services offered by Apple and Google as well, so you don’t need to trawl through data leaks manually yourself. Sections of the dark web are often closed down too, as part of police operations. Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges. (Presentation and polish isn’t quite so important on this part of the internet.) Click on any website link, and it’ll appear on screen, with its address at the top. SecureDrop has even been adopted by various news organizations worldwide. It provides a safe haven for anyone looking to shed light on wrongdoing or share critical information with the media.
Can Search Engines Find Everything On The Dark Web?
For the most security-conscious, you can even install the Tails operating system on a flash drive and run Tor from that. But despite its many benefits, it’s sadly just a matter of fact that the dark web can be a dangerous place. Near total anonymity and a complete lack of regulation can easily attract criminality, and onion sites can harbor malware such as ransomware or spyware.

Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook. This .onion link makes it impossible for hackers to impersonate your profile. This is the best place to get short and reliable links to an unalterable record of any webpage across government and corporate websites. SecMail is one of the most popular email services on the dark web. While this is not much compared to standard email services, it is enough for PGP-encrypted messages. Unfortunately, it requires you to have an invitation code to create an account.
You can run a dark web scan to see if any of your data has leaked onto the black market. And if you think you’ve fallen victim to identity theft or fraud, be sure to report the internet scam just like you would any other crime. But anything that’s against the law on the regular web or offline is also illegal on the dark web. This includes buying or selling illicit goods, illegal transactions, and downloading copyrighted material. Yes, you can access the dark web on a smartphone, but you’ll need an appropriate browser, like Tor browser for Android or Onion browser for iPhone.
OnionLand Search
It is a safe haven where anybody with information can share it anonymously and without fear of being tracked. What you may not know is that you can use Tor browser to access regular HTTPS websites on the surface web. This prevents tracking and fingerprinting, because Tor browser isolates each website you visit, meaning that third-party trackers and ad networks can’t follow you around. mark it means it has been verified as a scam service and it should be avoided. Radar Rundown Free firewall software allow privacy ethusuiasts to secure their network and block mal… We recommend installing a premium antivirus program for optimal protection against malware infections. We also made sure to select only sites that have been around for a considerable amount of time without being taken down or being the subject of any privacy or security scandals. If you wish to access the snapshots of these websites, just type in the domain name, and you will get the results depending on how many records exist on the website.|You can access onion sites only through the Tor browser or special network configurations. On the Tor network, the onion domain name reflects the fact that, like the layers of an onion, the Tor browser consists of layers of protection. Tor encrypts traffic, masks your IP address, blocks trackers and browser fingerprinting, and doesn’t store a record of your activity.|Thus, staying connected to a VPN when you access these sites is vital. Since you cannot access a library of dark web links using the regular Internet, you can check out platforms dedicated to indexing these sites, like The Hidden Wiki. This browser is the most suitable option for accessing the dark web, thanks to its multiple layers of encryption. Each time you connect to a dark web link, your request and traffic are routed through at least three different server points, ensuring your IP remains hidden. Because it’s a members-only platform, you’ll need to register first. Thankfully, you don’t need to use your official name or email; just use a fake username (we tested it successfully).|As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing. Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people. Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion.}
While it doesn’t index dark web content, it’s the default search engine on the Tor Browser because of its strong privacy features and lack of tracking. For searching within the dark web, specialized tools like Torch are better, as they specifically index .onion sites and hidden content. While they make accessing Tor-hidden websites easier without the Tor browser, they can compromise your privacy and security by acting as intermediaries that might expose your data.
For these reasons, it’s a good idea to safeguard your online activities with NordVPN while using the dark web. The platform utilizes end-to-end encryption, ensuring it does not store any activity records. Like other email clients on the dark web, it does not require you to give your personal information.
In addition, they share information of great importance, about the Tor network and the Tor project. However, not Evil is not a repository for illegal services and illegal material. Please note that not Evil does not tolerate adult content, narcotics / gun markets, or any other illegal content. There are a variety of illegal activities that take place on telegram channels including the sharing or sale of stolen data (credit cards, banking information, stolen credentials, etc.). While this list is not comprehensive, it is a short overview of the types of activity you might see on Telegram.