Companies use dark web monitoring to scan for leaked data, stolen credentials and breach indicators, helping them...
wpadmin
Often, these sites are made to look just like real, trusted platforms, such as banks, social media...
Tor routes your traffic through a chain of relays to obscure your IP address. This makes it...
The dark web is often confused with the deep web, but they are different. The deep web...
Accessing the dark web using equipment like the Tor browser doesn’t fall under criminal activity. Engaging in...
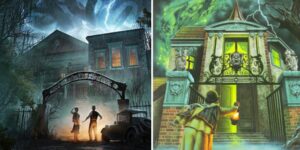
The dark web is a hidden part of the internet that requires specific software to access anonymously,...
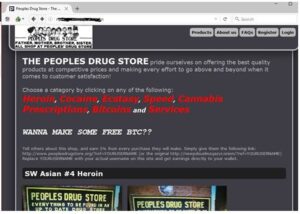
These sites are typically not listed on Google or other search engines. You can find them on...
“Pay-per-order” isn’t available, and advance deposits required to the marketplace wallets. Each deposit goes through its internal...
Not only that but I am scared about my private information being used and sold to companies....
Using open-source means there’s far less chance of any security flaws or deliberate backdoors as the code...