We hope this information will help you better understand and become more aware of the importance of privacy in the financial markets. In this way, Dash contributes to the realization of fast and low-cost transactions in the modern financial markets. This allows consumers and businesses to move funds more efficiently and plays an important role in supporting global economic activity.
- By relying on encryption, pseudo-anonymous currencies, and network-level anonymity, they create a false sense of safety, drawing in both buyers and sellers.
- The ability to understand and counteract its growth will define the future of cybersecurity and digital law enforcement.
- Cyber threat intelligence (CTI) helps organizations predict, understand, and defend against cyber threats, enabling proactive protection and reducing the impact of attacks.
- The most recent example is the shutdown of the oldest marketplace Hydra Market in 2022 which took a combined effort of the FBI and the German authorities.
Trends Shaping Dark Web Activity In 2025
These hidden digital spaces host a variety of illegal and illicit activities, from drug trafficking and weapons sales to data breaches and financial fraud. The decentralized, pseudonymous nature of cryptocurrencies has provided a strong foundation for these underground markets to expand, adapt, and resist law enforcement pressure. These platforms also often have built-in encryption for communications and transactions, making it hard for law enforcement to track down the individuals involved.
Dark Web Reveals Tech Companies Leak Most User Data

Consider checking community forums like Dread or darknet.fail for current status information, but only trust links verified by multiple reliable sources. Enable two-factor authentication whenever available, and consider implementing a dedicated system exclusively for darknet activities that remains isolated from your personal computing environment. Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation. Patterns recommended to avoid include hiring hitmen like Dread Pirate Roberts, and sharing handles for software questions on sites like Stack Exchange.
Understanding The Risks
Here, you can find anything from stolen credit card information and personal data to illicit drugs and counterfeit goods. Dark web marketplaces are infamous for being hotbeds of illegal activity, from selling malware and stolen data to offering all sorts of illicit services. Here, we’re going to look at the threats these dark web markets pose, explore recent law enforcement takedowns, and look at the strategies being used to track and tackle these shady activities. Alphabay Market leads with 60,000+ listings and $20 million in monthly trades via BTC and XMR, dominating 20% of darknet marketplaces.
A Brief Overview & History Of Darknets & Dark Markets
Abacus Market — once the largest Bitcoin-enabled Western darknet marketplace — went offline in early July 2025. TRM Labs assesses the event was likely an exit scam, though a covert law enforcement seizure cannot be ruled out. Arresting vendors often has a greater disruptive impact than taking down DNMs.
They employ various techniques, such as tracking and infiltrating dark markets, developing advanced threat intelligence, and enhancing international cooperation. As darknets and dark markets continue to evolve, understanding their dynamics and implications is crucial for fortifying the cybersecurity defenses of individuals, organizations, and nations in the digital age. Darknets and dark markets have fueled the growth of cybercrime, provided a marketplace for cyber threats, and expanded the attack surface for malicious actors.
History And Unique Features Of Dash
The 32-year-old main defendant, the suspicious men and possible other accomplices are said to be responsible for more than 6,000 sales with a turnover of more than 750,000 euros. The Bamberg Public Prosecutor’s Office spoke to the NDR Niedersachsen of investigations against a criminal network. According to the information, the searches and arrests already took place on the 9th. The Bamberg Public Prosecutor’s Office and the BKA did not make the case public until Wednesday. A spokesman for the Bamberg Public Prosecutor’s Office justified this with ongoing investigations.

Agentic AI In Cybersecurity: Transforming Threat Detection And Defense
- Quality and validity of the data it provides justify its higher cost over other marketplaces.
- It all started with a username on Dread forum called archetypleaked who claimed that he hacked the server of Archetyp Market and requested 100 XMR (Monero) in order to not continue exposing more information.
- A global network of masternodes vote on proposal for improving dash and approved proposals are funded from the treasury which receives 10% of all newly created dash.
- Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down.
Also, set up two-factor authentication (2FA) to add an extra layer of protection in case someone manages to figure out your password. Moreover, if you must use public Wi-Fi, ensure that you use a VPN to mask your browsing activity and keep yourself secure. The fact that there are no real regulations as well as authorities to monitor transactions, you’re always on your own, and you’re a potential target and victim of a scam or fraud. Who doesn’t like privacy, especially when dealing with the buying and selling of illegal products and services? Therefore, given the nature of anonymity and privacy of the dark web, several stores keep on emerging in the dark despite a continuous crackdown on several others.
This is why there’s no specific endorsement for any particular marketplace I can make, but I’ll include a few of the most common below for reference. It’s one of the largest darknet markets that launched in 2022 and trades sensitive financial credential transactions. It’s the place where you can buy or sell stolen credit card numbers, SSH login credentials, and personally identifiable information (PII). The stolen data can be just anything from full names, credit card details, passwords to social media accounts, bank account information, and social security details, among others. While there are legitimate products and services in the darknet markets, often, these markets deal with illicit goods and services like drugs, fake documents, and hacking services. Their presence can make you wonder why darknet markets and not just the regular online stores.
They can only be accessed through the Tor browser, which encrypts your connection and masks your IP address, providing anonymity. Ethically, they must minimize harm, responsibly handle any stolen or sensitive data (often notifying victims or law enforcement), avoid entrapment, and maintain research integrity. With over 20 years of experience in cybersecurity and marketing, Ben has held leadership roles at companies like Check Point, Cognyte, Cylus, and Ionix. Darknets also serve as a platform for whistleblowers and privacy advocates. Platforms like SecureDrop enable individuals to submit documents and communicate securely with journalists, thereby exposing corruption and wrongdoings while preserving their anonymity. The significance is in safeguarding the right to free speech and the role of the press as watchdogs.
Thor Platform Capabilities And Market Functions
Tailored for targeted infection, these high-end cryptors provide advanced invasive capabilities for bypassing runtime protection by security solutions. Keeping an eye on the dark web is no easy task, but law enforcement and cybersecurity pros have some pretty advanced tools up their sleeves. The same way criminals use tools to sort through stolen data, law enforcement uses advanced data analytics to sift through vast amounts of information, looking for patterns and connections that might point to illegal activities. Machine learning is another big player here—it helps by analyzing data to predict and identify suspicious behavior much faster than a human ever could. Many darknet marketplaces employ the use of specific cryptocurrencies (such as XMR) that use technologies such as stealth addressing and ring signatures to evade traceability.
Prioritize Escrow
This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself. Litecoin, Zcash, and Dash also see usage, though Monero and Bitcoin dominate the dark web. Some marketplaces have even mandated Monero-only transactions, underscoring a strong preference for privacy-focused coins over traceable ones. It has a bidding feature, with new batches of stolen data being frequently added. Active for a decade since 2014, it is a widely used credit card shop used to source stolen credit card information such as dumps, CVVs, Wholesale Accounts. The Abacus Market links to the new dark web marketplace sections and took over much of the vacuum left by the AlphaBay takedown.
Its 9,000+ users and 700+ vendors focus on drug trades with strong escrow security. Providing secure, anonymous access to a wide range of products through the Tor network since its inception. Darknets and dark markets present a multifaceted challenge to businesses and society as a whole. While these hidden networks can be used for legitimate purposes, they are equally significant as vectors for cybercrime and illicit activities. Accessing darknet markets safely isn’t just about the tools you use — it’s also about the way you behave online. By following simple but effective OPSEC strategies, you can protect your identity, avoid scams, and reduce unnecessary risks.
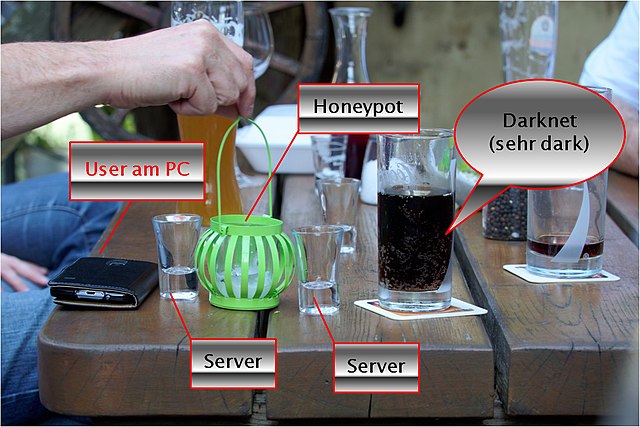
We’ve got a long road ahead, but with collective effort, we can make a real difference in the fight against cybercrime. Undercover operations are also vital for these operations, with agents posing as buyers or sellers to infiltrate these markets. Digital forensics helps in tracing digital footprints back to their sources. Tor establishes a secure network circuit for each browser session, which connects Tor nodes deployed around the world at random. These nodes encrypt your browser traffic in layers at each node hop on its way to/from the source (your browser) and the destination (a hosted hidden service).