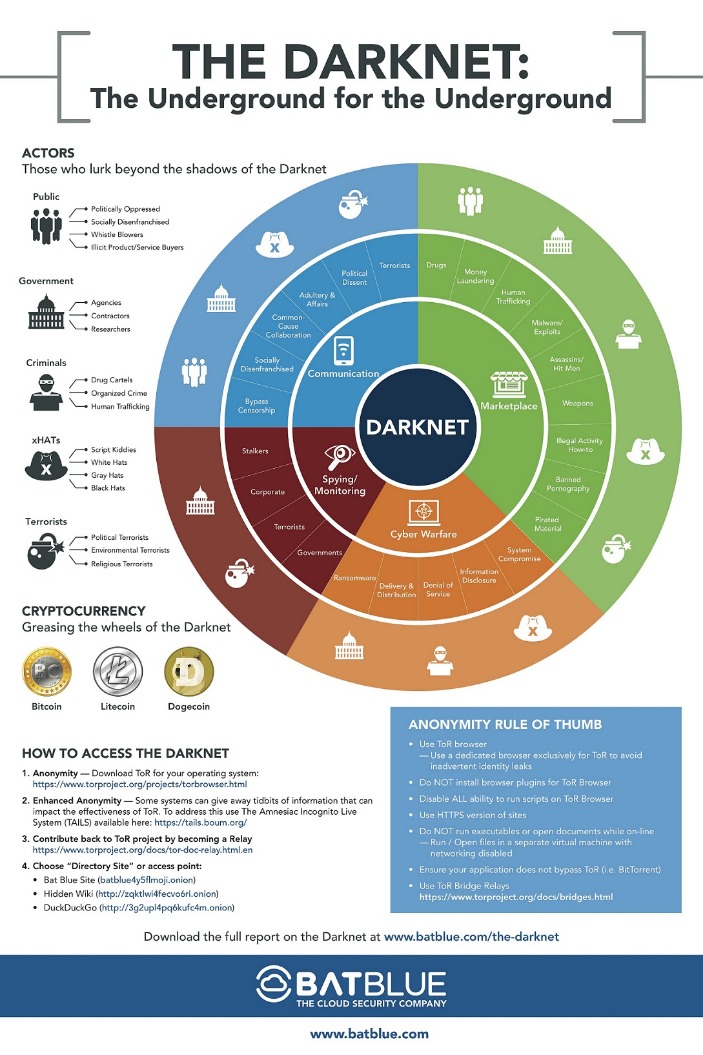
Most dark markets have user review systems and vendor ratings to establish trust. Law enforcement regularly shuts down these markets, but new ones continuously emerge. Fentanyl sales on the dark web have been a major focus of U.S. law enforcement. Other potential illegal activities include identity theft, blueprint distribution, human trafficking, and weapon sales. The FBI’s 2013 crackdown on the Silk Road marketplace, an online narcotics bazaar, was a high-profile response to a large operation, the report noted.
Darknet Markets And OPSEC: Essential Cybersecurity Practices For 2025
Since its inception in 1992, the task force has been responsible for the seizure of approximately $600 million and more than 2100 arrests. The darknet is a mysterious and often misunderstood part of the internet, attracting both intrigue and concern. Darknet markets, in particular, have gained attention for their role in facilitating the exchange of illicit goods and services.
Privacy Protection
It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. No user names are tied to actual identities, and no moderation like one may find on Reddit. Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities.
- Dark web marketplaces are websites where you can exchange illicit goods and services like stolen credit cards, account login credentials, counterfeit items, drugs, and other items.
- One of the biggest recent successes was the takedown of Hydra Market, considered one of the largest dark web marketplaces.
- It allows you to search for images, maps, files, videos, social media posts, and more.
- Corporations and governing bodies alike currently participate in unauthorized surveillance of online activity.
- Fake online casinos and social networks are common methods for distributing malware.
Recently, European law enforcement agencies conducted an operation codenamed SpecTor, which resulted in the closure and arrest of the suspected operators of the Monopoly Market, a very successful, esteemed and renown market at the time 15. Darknets and dark markets have propelled the growth of cybercrime by offering a platform for the sale and exchange of malicious tools and services. Cybercriminals use these platforms to traffic in stolen data, execute targeted ransomware attacks, and collaborate on advanced hacking techniques.
How KELA Cyber Supports You In Darknet Monitoring And Risk Mitigation
Nation-state actors, too, leverage darknets for espionage and cyber warfare, capitalizing on the obscurity and untraceability they provide. The darknet remains a critical area for cybersecurity professionals, journalists, and law enforcement due to its role in illicit trade, intelligence gathering, and cybercrime. With platforms like Dread providing updates on darknet market activities, understanding operational security (OPSEC) and defensive techniques is crucial. This article covers key cybersecurity commands, tools, and strategies to navigate and secure systems in this high-risk environment.
Crime Identification
Law enforcement officials are getting better at finding and prosecuting owners of sites that sell illicit goods and services. In the summer of 2017, a team of cyber cops from three countries successfully shut down AlphaBay, the dark web’s largest source of contraband, sending shudders throughout the network. Taking down criminal websites hosted on the darknet is notoriously difficult as the location of their servers are often hard to find or in jurisdictions that do not respond to Western law enforcement requests, like Russia.
- This is the best place to get short and reliable links to an unalterable record of any webpage across government and corporate websites.
- In response, cybersecurity professionals, law enforcement agencies, and policymakers around the world are working to combat this growing menace.
- Deep web refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google.
- In fact, WeTheNorth is more of a private club than an open market – something its operators want.
- These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies.
Enable The TOR Service To Start Automatically
We believe this aligns with the long-standing trend that scamming is most successful when markets are up, exuberance is high, and people feel like they are missing out on an opportunity to get rich quickly. Of course, the impact of romance scams on individual victims is devastating and should not be understated. And while increased reporting – at least in the U.S. – is a good sign, we still believe insights into romance scams in particular suffer from underreporting.
Enter A Darknet Web Address
It is easily accessible by the general public and requires no special configuration. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. The dark web is part of the internet that is not indexed by standard search engines like Google, Yahoo, and Bing. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data.

We wonder if we can design a crawler that can use an adaptive method to adjust the request rate dynamically instead of a set of predetermined values or a range of values. This is a more traditional security mechanism that states that the market is still controlled by specific operators. This statement (canary) is usually displayed on a page in the market and is signed with the operator’s Pretty Good Privacy (PGP) signature.

As cyber-criminals embrace new technologies it’s becoming increasingly necessary for security professionals to do the same in order to stay ahead. OSINT tools allow security professionals to effectively and efficiently monitor the surface deep, and dark web. Using Signal you can create targeted searches with Boolean logic, and then run the results through intelligent filters powered by our advanced AI. According to Webhose, one of our data providers, there are approximately 20 active leading dark web marketplaces and there are dozens of smaller additional marketplaces.
The dark web has flourished thanks to bitcoin, the crypto-currency that enables two parties to conduct a trusted transaction without knowing each other’s identity. “Bitcoin has been a major factor in the growth of the dark web, and the dark web has been a big factor in the growth of bitcoin,” says Tiquet. Ransomware-as-a-service (RaaS) kits have been available on the dark web for several years, but those offerings have become far more dangerous with the rise of specialized criminal groups like REvil or GandCrab. These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”.
Dark markets continually adapt and evolve to stay ahead of law enforcement and security measures. This ongoing cat-and-mouse game poses a significant technical challenge in combating the activities within darknets. In this system, cryptocurrency is held by a trusted third party until the buyer receives the product or service as described. Once the buyer confirms satisfaction, the funds are released to the seller.