People use dark markets when they want extra privacy and anonymity. Many users value the protection that comes with keeping their identity hidden. This secure setup is useful for those who want to avoid government surveillance or keep their personal information safe from online threats. If you’re interested in marketplaces, start by learning about the top darknet markets. These platforms are hubs for various services and goods, and understanding their features is key to navigating them safely. The platform’s interface is a trader’s dream, with advanced filters, real-time tracking, and vendor ratings averaging 4.8/5 across 50,000+ reviews.
Vet Vendors Thoroughly
It also comes with identity theft insurance, which can help cover the cost of recovering from identity theft. Always verify links through trusted sources like Dread or PGP signatures to avoid phishing. Check around with other users and ask if they know anything about the new marketplace. These high levels of anonymity increase the opportunity for the “bad guys” to sell drugs, stolen IDs, credit cards, weapons, and many more compromised products or information. The last thing you need to do is to start researching vendors and determine what marketplace is a possible vendor to buy the products from. From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains.
Dark markets continually adapt and evolve to stay ahead of law enforcement and security measures. As one marketplace is taken down, another often rises in its place. This ongoing cat-and-mouse game poses a significant technical challenge in combating the activities within darknets. Dark markets include features similar to those found in legitimate e-commerce platforms, such as product listings, user reviews, ratings, and customer support. These features help create a sense of ‘trust’ among users, even in the criminal ecosystem.
- Bitcoin and Monero flow smooth; their updates kept a crash at bay last month.
- Vice City uses AES-256 with PGP, optional 2FA adopted by 50% of its 9,000+ users, and basic DDoS protection for 92% uptime.
- There are several other browsers you can use, such as Freenet and I2P, but Tor is the most recommended option.
- For instance, the Ashley Madison data dump was posted to a site only accessible to Tor users.
- If this is selected, your PGP key will expire on the specified date.
Title: Understanding Decentralized Marketplaces On The Darknet: A Comprehensive Guide
It’s essential to use a VPN, like Forest VPN, to secure your data, avoid clicking on unfamiliar links, and never disclose personal information. Additionally, using antivirus software and strong passwords can further protect you from potential threats. Discover how to explore darknet market links safely while ensuring your privacy and security.

Welcome To Your 2025 Darknet Markets Guide

To stop the marketplaces is not a walk in the park as it takes immense effort from authorities like the FBI and international law enforcement. The dark web is only accessible through specific software like Tor (The Onion Router). Also, while this huge portion of the internet has a reputation as home to nefarious activities like hacking and drug trafficking, it also harbors legitimate activities like journalists and whistleblowers. From state-sponsored groups to ransomware gangs, criminal activity is innovating at a rapid pace on the dark web. Businesses must stay vigilant and proactive in addressing these threats, using tools like CybelAngel to monitor dark web activity and protect their assets. The Tor project gained notoriety for enabling illegal marketplaces like the Silk Road, a black market taken down by the FBI in 2013—and countless cybercriminal service providers ever since.
The legality depends on your activities and your country’s specific laws regarding darknet use. Dark markets provide a one-stop-shop for cybercriminals, offering a wide range of services such as hacking tools, stolen data, ransomware, and Distributed-Denial-of-Service (DDoS) attacks for hire. This increases the accessibility and sophistication of cyber threats, with far-reaching consequences for businesses.
- Also, there’s a vast amount of unsavory content on the dark web, as well as a significantly high number of hackers and scammers looming on the platform.
- These rankings highlight the heavy hitters among hidden trading platforms, focusing on the most influential Tor-based marketplaces steering the deep web trade scene.
- One of the most common risks when accessing darknet markets is ending up on a fake or cloned site.
- Transactions on dark market URLs are typically conducted using cryptocurrencies, such as Bitcoin, which further obscures the identity of the parties involved.
- One of the most popular uses of the darknet is for online marketplaces, also known as darknet markets or DNMs.
- This guide provides official Abacus links, mirrors, and security tips to help you navigate the market safely.
Q: How Do I Safely Send Coins To A Market?
Darknet Markets are online marketplaces where people can buy and sell illicit goods and services under the protection of the anonymity by TOR. The products that are most commonly listed for sale include drugs, fake documents, fraud-related items, and hacking services and tools. Markets like AlphaBay and Hansa adopted stronger encryption and expanded offerings to include hacking tools and stolen data. However, these platforms often faced law enforcement takedowns, technical issues, or exit scams, where operators vanished with user funds. Darknet marketplaces emerged around 2011, with Silk Road setting the standard for how these platforms operate.
Incognito Market Vendors
What sets this guide apart is its depth—beyond just rankings, we’ve woven in historical angles, user thoughts, and hard numbers for a full picture of each market. Together, these ten markets handle over $50 million in monthly trades, showing their clout in the hidden economy. Keep reading to uncover the stories, stats, and tactics behind these top-tier trading hubs shaping the underground scene in 2025.
Tech Keeping Darknet Markets Alive
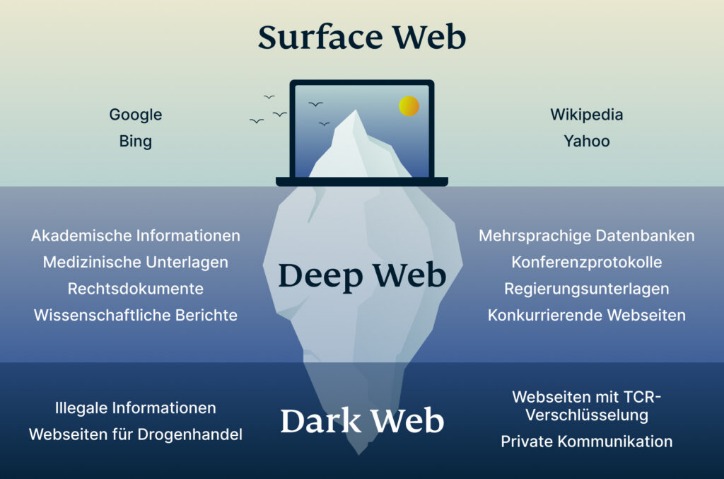
Did you know that Google only shows you a glimpse of all the websites that actually exist? The last time I checked, it’s estimated that the entire web is roughly 500 times larger than what Google returns in Google Search. There are a few reasons why the dark web isn’t stopped or shut down. First, it’s difficult to track and monitor activity on the dark web since much of it is encrypted. One of the great things about Tor is that it can be used to access both the dark and surface web.

It is home to all sorts of disturbing content, given that the markets share content related to non-consensual recordings and child exploitation. Who doesn’t like privacy, especially when dealing with the buying and selling of illegal products and services? Therefore, given the nature of anonymity and privacy of the dark web, several stores keep on emerging in the dark despite a continuous crackdown on several others. For example, the CIA has a dark web site for anonymous reporting services.
Infostealer threat actors specialize in malware that harvests personal data without consent, such as login credentials, bank accounts, and social security numbers. Their tools often spread through phishing campaigns or compromised software downloads, enabling crimes such as identity theft. In conclusion, choosing the right darknet market requires careful consideration of various factors, including security and anonymity, product selection, user experience, and customer support.

Method II – VPN Over Tor
It might sound weird that Google doesn’t index these pages, but it does carry some logical sense. Google’s purpose is to show the most relevant information to all of its users quickly and easily. That means that Google wants to minimize the amount of time users spend searching for certain queries.
We offer a seamless, secure, and trusted experience tailored for the Canadian community. It offers outstanding privacy features and there is currently a discounted rate available through this link. Also, there’s a vast amount of unsavory content on the dark web, as well as a significantly high number of hackers and scammers looming on the platform. This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware. Tails also protects you from possible malware, viruses, or keystroke loggers that may have already infected the computer, as it doesn’t run the operating system already installed on the device. Tails is a mere 1.3 GB download, so on most connections it will download quickly.