The majority of the users on the dark web use the Tor (The Onion Router) browser. A vast number of URLs have domain endings such as “.onion”, which means that the URLs are only accessible by Tor users. It has been estimated that a large percentage of dark web traffic is related to illegal pornography that includes underage victims. Hacker services against banks and other financial institutions are offered there. We’ve also previously mentioned the “dark users” that use the dark web for illegal reasons, but the less said about them, the better. For example, the deep web is often a platform used by political activists who own a blog.
Market Types
- The information that comes from a breach can be the same or similar as what comes from a Leak, but the method of obtaining said data is by direct attack instead of undisclosed vulnerability.
- Moreover, the absence of a central authority – like a bank or government – overseeing these transactions makes it more challenging to monitor and regulate this activity.
- Bitcoin’s rising transaction fees are the primary reasons for the switch.
- Dark web marketplaces provide a platform for illicit transactions, often favoring cryptocurrencies such as Monero, known for its enhanced privacy and anonymity.
- This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page.
E-commerce vendors on the dark web, a place where the cryptocurrency remains unchallenged as the medium of transaction, have begun accepting other coins. Acronym for Society for Worldwide Interbank Financial Telecommunication; messaging system used by financial institutions to transfer money and comunicate financial transaction information securely. Otherwise known as private key; Large numerical value used to encrypt and decrypt data and is only shared with those that should have access to said data.

However, in April 2022, this site went offline after American and German federal government law enforcement agencies seized the website servers. Some alternative links are available, providing access to the marketplace. It’s recommended not to use new alternative links as they could just be planned exit scams.
Mitigating Risks In Crypto Transactions
Slow transaction times are frustrating as is but they are that much more disconcerting for those users who use them to purchase something illegal from the darkweb. Apart from the increased fees of completing the transactions, the time for confirmations was also increasing substantially. Hence, vendors had to institute a rule that they would wait for three confirmations on the network before concluding the sale was complete. Bitcoin remains the primary payment currency of the dark web, accepted across all marketplaces and forums. However, alternative coins have been added recently, among which Litecoin is dominant. As with any business agreement, speed of payment completion is crucial — this is especially true for the dark web.
Law enforcement agencies around the world are cracking down on illicit activities conducted through cryptocurrency transactions. Governments are implementing stricter regulations, mandatory reporting, and Know Your Customer (KYC) policies to curb money laundering and illicit transactions. While these efforts aim to increase security and reduce illegal activities, they may also limit the privacy and anonymity that cryptocurrency offers on the dark web. In summary, the use of cryptocurrency, particularly Bitcoin and Monero, has revolutionized transactions on the dark web. The convenience, trust, and anonymity provided by these digital currencies have made them the preferred choice for illegal activities on hidden web platforms.
ToolShell Deep Dive: The SharePoint Exploit Crisis Uncovered
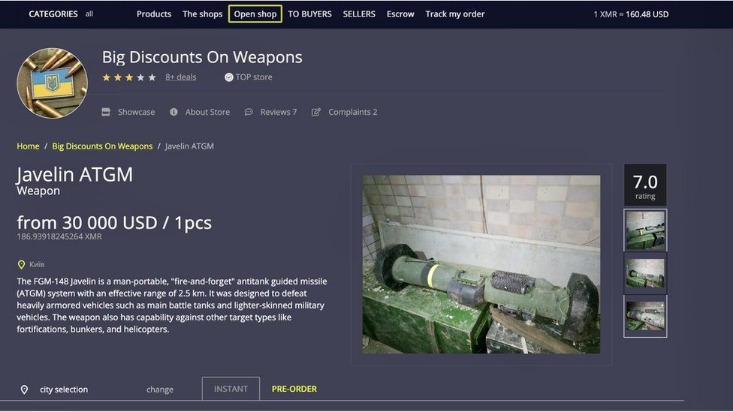
As law enforcement agencies crack down on illegal activities on the dark web, money laundering schemes utilizing cryptocurrencies emerge as a growing concern. Cryptocurrency, particularly Bitcoin and Monero, plays a significant role in facilitating transactions for illicit goods and services. The most popular items purchased with cryptocurrency on the dark web are drugs, such as cannabis, cocaine, and MDMA. However, the dark web marketplace also offers a wide range of illegal offerings, including stolen credit card data, hacking tools, and counterfeit identities. While weapons are available for purchase, they represent a smaller market due to their accessibility outside of the dark web. Abacus Market appeared on the scene in 2021 and quickly became one of the heavyweights among English-speaking markets on the dark web.
Facebook Onion Site
Litecoin (LTC) is a cryptocurrency that was designed to provide fast, secure and low-cost payments by leveraging the unique properties of blockchain technology. You can conduct discussions about current events anonymously on Intel Exchange. There are several whistleblower sites, including a dark web version of Wikileaks. Pirate Bay, a BitTorrent site that law enforcement officials have repeatedly shut down, is alive and well there. In addition, VASPs can work with regulatory authorities and share information to aid in investigations and enforcement actions.
Often entails the illegal use of a credit card by an unauthorized person to purchase a product, good, or service. You can buy credit card numbers, all manner of drugs, guns, counterfeit money, stolen subscription credentials, hacked Netflix accounts and software that helps you break into other people’s computers. Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account.
What Is The Main Cryptocurrency Used On The Dark Web?
Nevertheless, it managed to defraud users of over $4 billion through Ponzi scheme tactics and multilevel marketing strategies. These cases underscore the importance of vigilance and due diligence when dealing with virtual currencies and money laundering. Other dark web search engines worth investigating are Ahmia, Torch, NotEvil, and the Onion URL Directory—just type out some keywords for what you’re looking for. Some of these sites can be found through regular web browsers, but you’ll then need to switch over to Tor once you’ve got the onion links you want to follow. And yet, what Monero might be best known for in the general public is its now-common usage in illicit transactions.
When one goes down, two more emerge with new ideas, better technology, and greater difficulty to track. It’s an ever-evolving ecosystem—constantly shifting, reinventing itself, and adapting. Some platforms have begun to operate exclusively with this confidential coin.
Technologies And Tools Commonly Used In Dark Web Black Markets
At the same time, as these currencies become more readily available to a general population, malicious tools such as ransomware will also continue to evolve to take advantage of the mainstream trend. Bitcoin’s rising transaction fees are the primary reasons for the switch. The report’s authors claim that high fees have made it “economically unfeasible” for use on the dark web, where most daily transactions are usually in small amounts. Bitcoin’s congested blockchain and high transaction fees have claimed another casualty. Website that allows registered users to collaboratively write and edit content directly for all users to be able to see.
The Role Of Cryptocurrency On The Dark Web
They may lack adequate security measures to protect user funds and personal information. Even when crypto platforms comply with high KYC standards, some users can still circumvent those controls, making them vulnerable to various attacks and potential loss of funds (IDnow). The Financial Action Task Force (FATF) is a global entity that drives the effort to combat money laundering.
In addition to the darknet markets, XMR has also become a rising star in ransomware. Experts say ransomware actors are increasingly demanding ransom payments in Monero, and some even charge less if a victim pays in the coin. Of course, there are other reasons that restrain the process of legalization, related to tax issues, money laundering, ICOs and investment risks. The term “darknet” first appeared in the 1970s and referred to the private networks with a high degree of confidentiality.
The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe. You can either sell or buy goods on the dark web, but both present difficulties. Unfortunately, it’s also a place where the bad guys can offer their services – for example, hackers or hitmen. In opennet mode, the network will automatically assign you to other users on Freenet’s network.