You might want to hide your Tor Browser download using a VPN and your existing browser’s private/incognito mode. Our rigorous research and testing have revealed revealing truths and busted myths. We’ll navigate this intricate maze with you, uncovering its secrets while ensuring your online safety. The US government created the dark web to help its spies communicate and exchange information securely.
Email Services
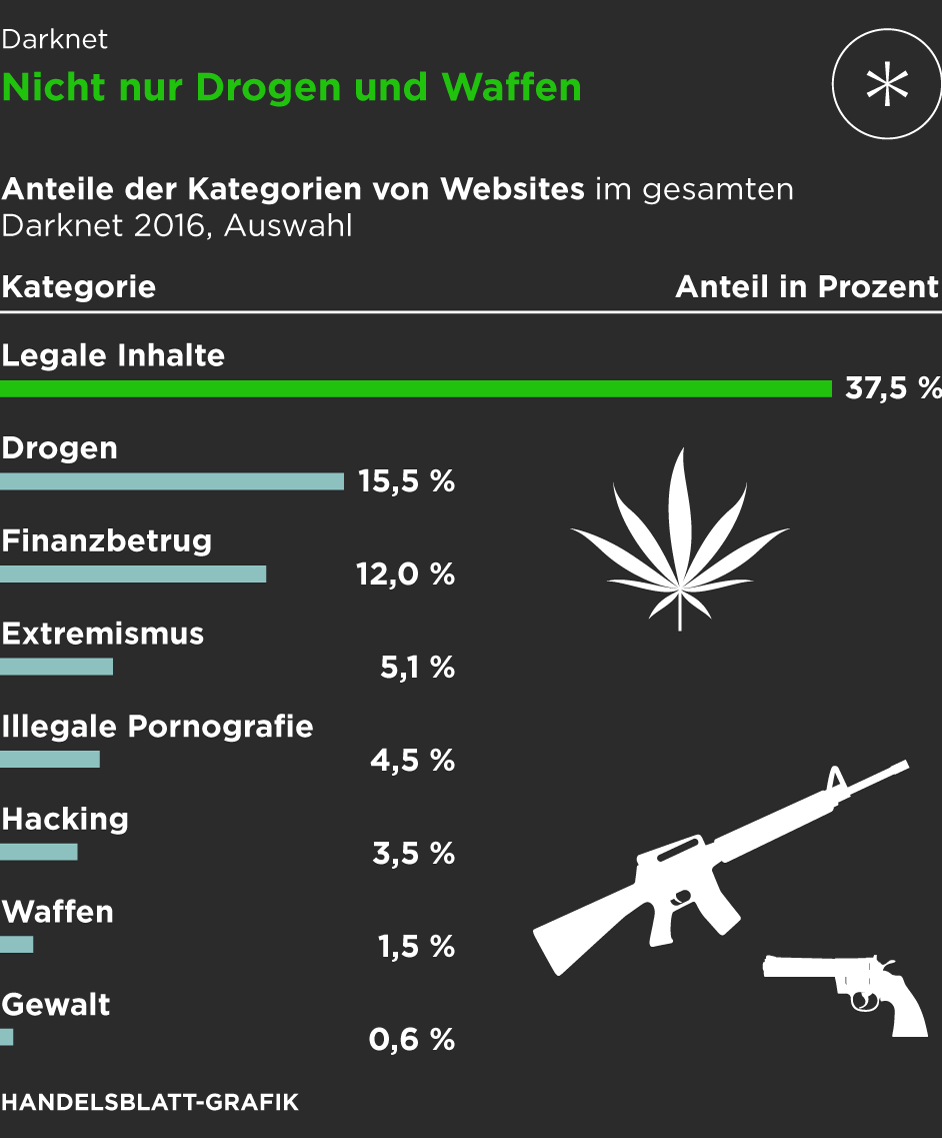
Around this time, one of AlphaBay’s administrators, Alexandre Cazes, made a series of mistakes, exposing his identity. Operation Bayonet, a multinational law enforcement operation, pounced and shut down AlphaBay, arresting Cazes, who was found dead in his cell weeks later. Dark web drug sales—which form the majority activity there by volume—represent a small but growing portion of the total worldwide drug trade. Exact numbers are difficult to pin down, but the United Nations Office of Drugs and Crime estimates that such drug sales quadrupled in size over the past decade, reaching $315 million.
What Types Of Marketplaces Can You Find On The Dark Web?

In fact, the Guardian referred to darknet markets as “the eBay of drug dealing,” and rightly so, illegal drugs are found in almost all the shops on the dark web. People use dark markets when they want extra privacy and anonymity. Many users value the protection that comes with keeping their identity hidden. This secure setup is useful for those who want to avoid government surveillance or keep their personal information safe from online threats.
- You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom.
- Businesses should be aware of the potential for data leaks and invest in data loss prevention measures.
- If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need.
- The use of encrypted messaging and secure payment methods ensures that transactions remain private and secure, fostering a thriving environment for trade.
- Unlike regular browsers that directly connect to websites via your ISP’s DNS, Tor anonymizes your journey by routing your request through several relays before reaching its destination.
- These advancements will further solidify their position as a secure and reliable option for users worldwide.
ProPublica is a popular online publication that won five Pulitzers in 2016. It aims to expose abuses of power and betrayal of public trust through investigative journalism. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see. Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. Purchases through links on our pages may yield affiliate revenue for us.
#1 – Silk Road 30
Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found. Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material. Site operators can also submit their own .onion sites for indexing. Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them. The dark web, which is what I’m discussing here, is a small subset of the deep web, and refers to websites that are specifically trying to stay out of sight. We do not condone, nor encourage, you to engage or interact with illegal activity found on these Dark Web marketplaces, and if you do, you do so at your own risk.

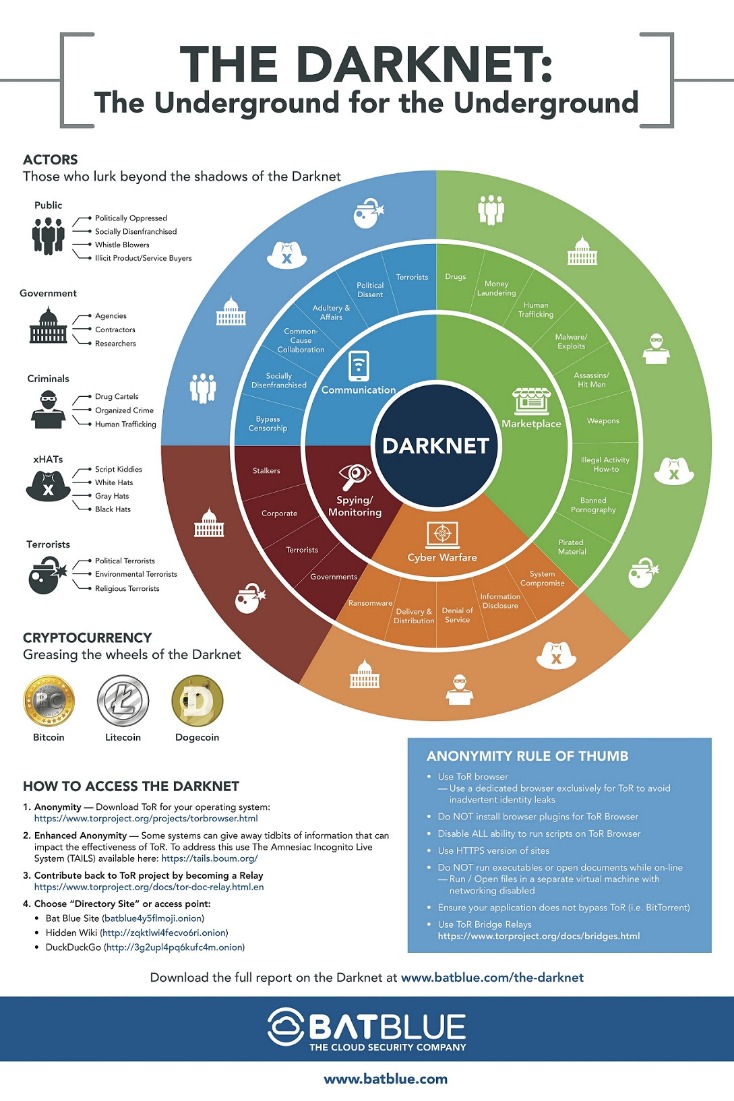
Lastly, the dark web is also used by activists and revolutionaries (like Anonymous). The dark web serves as a platform where activists can organize gatherings in secret, without the fear of giving away their plans or position to the government. Especially for these people, the dark web is the perfect platform to communicate and publish information without having to worry about imprisonment or any other form of retribution. The purpose was to protect U.S. army soldiers and agents in the field, but also politicians who held secret meetings and conversations, which contained the highest security measures. Those who access the dark web do so via the Tor (The Onion Router) browser.
Which Darknet Markets Are Still Open
Although content on the dark web is not as ‘indexed’ compared to the one on the clear web, you can still use search engines to find stuff. If you’ve ever checked your medical results online through a portal that required a login, you were navigating the deep web. It’s huge, making up about 90% of the internet, but it’s mostly mundane, hidden behind login screens for privacy and security.
Farwa is an experienced InfoSec writer and cybersecurity journalist skilled in writing articles related to cybersecurity, AI, DevOps, Big Data, Cloud security, VPNs, IAM, and Cloud Computing. Also a contributor on Tripwire.com, Infosecurity Magazine, Security Boulevard, DevOps.com, and CPO Magazine. Always use a fake name and a temporary email address when you buy something from dark net shops. You can even use a secure email provider or a burner email address whenever you visit the dark web. It doesn’t use JavaScript, meaning the website won’t track your activities or exploit vulnerabilities. The website allows a personalized searching experience, where you can search according to your geographical location, country-specific, and keyword or price-specific search results.
Cannazon Darknet Market

You can conduct discussions about current events anonymously on Intel Exchange. There are several whistleblower sites, including a dark web version of Wikileaks. Pirate Bay, a BitTorrent site that law enforcement officials have repeatedly shut down, is alive and well there. These high levels of anonymity increase the opportunity for the “bad guys” to sell drugs, stolen IDs, credit cards, weapons, and many more compromised products or information.

What Is A Darknet Market?
If you plan to purchase on a dark net marketplace or dark web commerce sites, you’ll need to create a fake identity. Remember only to make purchases using digital currencies and never provide any online banking login details. If you get a reliable vendor, you should procure the services to stay safe when accessing the dark web. You can also run a dark web scan to see if your information has been leaked on the dark web.
It was suspected as an exit scam; however, a few days after it had gone offline, it was revealed that AlphaBay had been seized and alpha02, aka Alexander Cazes, was caught. Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape. The experience is reminiscent of searching the web in the late 1990s. Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query. Link lists like The Hidden Wiki are another option, but even indices also return a frustrating number of timed-out connections and 404 errors. These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”.
The tool scans the dark web marketplaces and forums for signs of compromised personal credentials. The most recent example is the shutdown of the oldest marketplace Hydra Market in 2022 which took a combined effort of the FBI and the German authorities. Unfortunately, that as well didn’t stop other darknet markets from rising. Ever since Silk Road went down, several dark web marketplaces have kept coming and several of them shut down again. To stop the marketplaces is not a walk in the park as it takes immense effort from authorities like the FBI and international law enforcement. Discover everything about what is a darknet market, how it works, security threats related to it, and learn how to protect your data online.
How Did The Silk Road Work?
I2P uses one-way tunnels, so an eavesdropper can only capture outbound or inbound traffic, not both. The big downside is that your ISP will know you are using Tor, which is cause for concern in some places and will put many people off using this method. In this instance, too, it is important to use a logless VPN and pay with Bitcoin if you can to stay anonymous.
- We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal.
- You could be monitored closely even if you are not doing anything illegal.
- It helps us stay more vigilant, better protect ourselves, and make informed decisions online.
- It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals.
- Fresh Tools Market has become a go-to platform for cybercriminals seeking access to malicious software such as keyloggers, Remote Access Trojans (RATs), and ransomware-as-a-service.
- There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks.
ICE HSI opened an investigation to look into the specific source of the drugs. There was much information to disseminate; in almost three years of operation, more than 1.5 million transactions took place. We strongly recommend confining all surfing to the surface web—and help secure your data, online identity, and devices with a multi-layered solution like Avira Free Security. It blends performance, online privacy, and online protection into a single (free!) app. The integrated Software Updater, VPN, Password Manager, and more, create the convenient and trusted foundation on which to build a safer digital life. Malware is also easily available for purchase and is used by cybercriminals to access account details or for activities such as cryptomining.