These stolen cards have value because they can be used to purchase high-value items or gift cards, which can then be resold for cash. While browsing online, you might have noticed that the websites you are visiting have URLs starting … It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder. It is a relatively new provider but offers better features than most established VPNs. The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers. NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites.
- For instance, you can choose the preferred security levels for enhanced protection.
- Once your information is out there, you will likely experience more frequent social engineering attacks and these attacks will likely include more personalized information.
- Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security.
- Moreover, the layers of encryption and the bounce of your data from node to node effectively mask your IP address, enabling online anonymity.
- All that one can expect from a deep web marketplace when it comes to anonymity and security.
The Role Of Forest VPN
Upon investigating items for sale, ZeroFox noted it was commonplace for adult websites to be present, providing a possible social engineering angle for vulnerable individuals. Our regional data reveals that most people buying stolen credit card data on UNICC are from North America (after Global), while most of those selling it are from China. While it’s difficult to say exactly why that is, it’s possible that more criminals from China have the technological proficiency to steal credit card data. It’s unclear from research which these accounts are offered for, but historically we have seen them used for both.
Can You Be Traced On Tor?

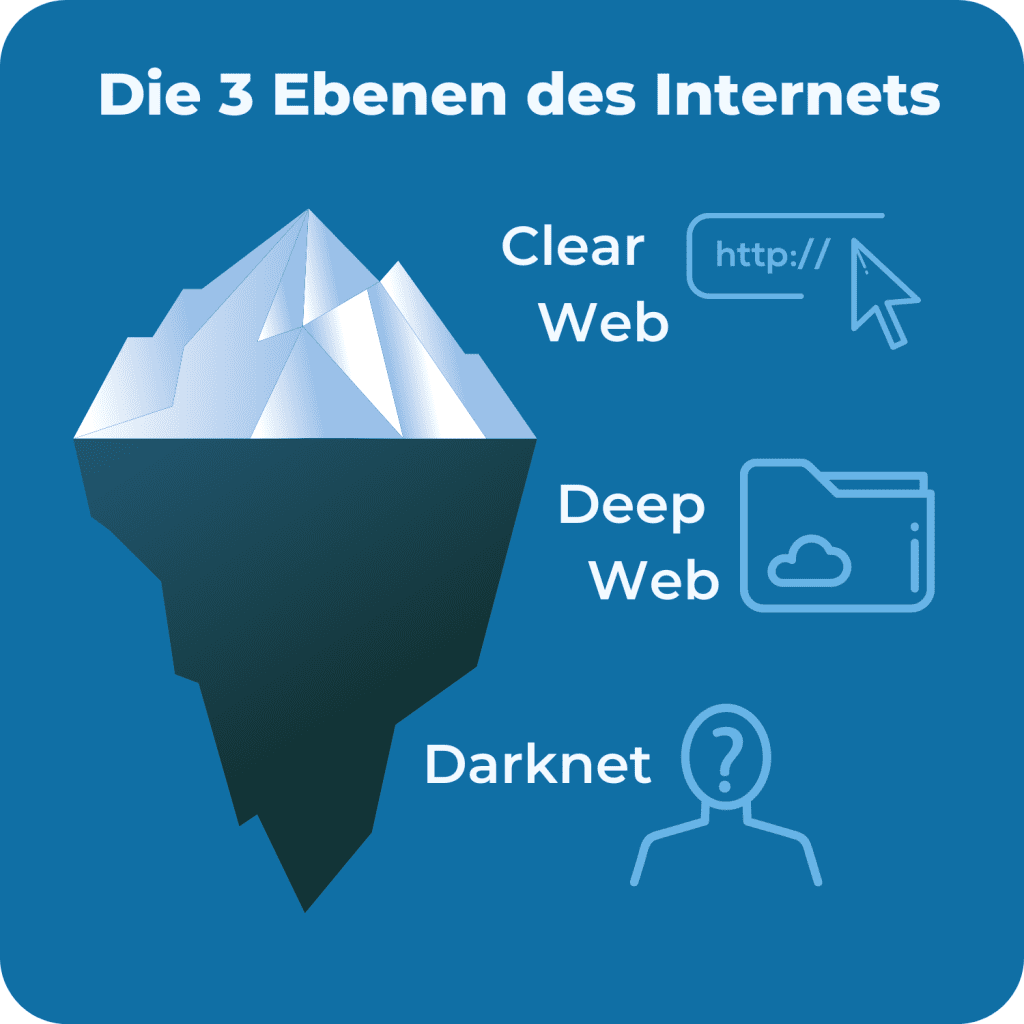
KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet. The readers like you support Beencrypted to help keep up the good work. When you purchase using links on our website, we may earn an affiliate commission at no extra cost to you. Organizations need automated dark web monitoring to prevent cyberattacks. One of the distinguishing features of Fresh Tools Market is its focus on providing up-to-date, freshly obtained tools and credentials. Bohemia entered the dark web scene in May 2021, quickly rising due to its modern interface and strict rules that reduce the likelihood of scams.
It provides an .onion URL and an interface for you to manage your Tor site easily. It also boasts that no personal information is required to use the service, and payment can be made with cryptocurrency. The Abacus Shop is the heart of our platform, offering a curated selection of over 5,000 products across various categories. In 2025, we expanded our vendor network to include over 450 verified sellers, ensuring a diverse and reliable inventory.
How To Effectively Communicate Cyber Risk To The Board: Lessons From APRA Compliance
Bohemia is a modern dark web marketplace with a great user interface that is easy to use and navigate. It asks you to pay the merchant fee if you want to sell something, preventing the buyers from getting scammed. World Market is another largest dark web shops that deals with various goods and services.
How To Access Abacus Darknet Market?
Operation SpecTor also resulted in the seizure of €50.8 million ($53.4 million) in cash and virtual currencies (possibly Monero), 850 kg of drugs, and 117 firearms. Archetyp was founded in May 2020 as an online marketplace to facilitate the illicit drug trade.17 It did not host other black market listings such as those for firearms or prostitution. Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring. Axis Intelligence provides dark web surveillance solutions that help businesses identify leaked credentials, fraud attempts, and malware risks before they escalate.
Should I Use A VPN When Accessing Darknet Markets?
- You should never use your personal information on the dark web anywhere else in your life.
- This focus on privacy makes it the Tor Browser’s default search engine and one of the best onion search engines.
- What distinguishes Thor from conventional marketplaces is its comprehensive approach to both technical and operational security.
- Its 9,000+ users and 700+ vendors focus on drug trades with strong escrow security.
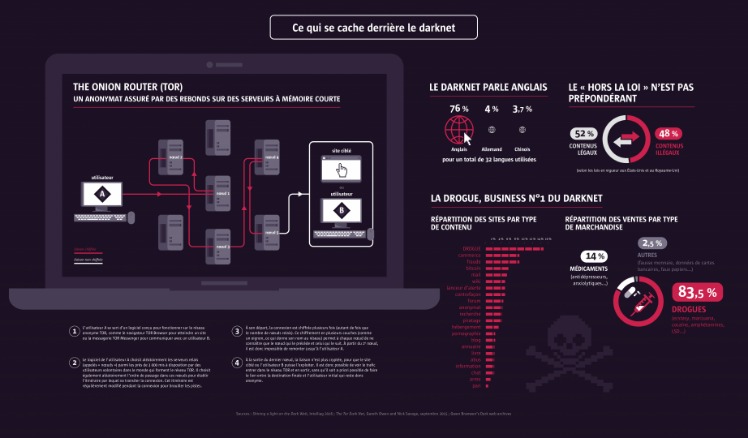
- Utilizing The Onion Router (Tor) network, these sites encrypt user data, providing layers of protection much like an onion.
With 12,000+ users and 900+ vendors, it boasts a 95% vendor rating—ideal for quality-focused dark pool trading. Usually, criminals sell access to exploits and stolen data, but increasingly sites such as 0day.today are releasing more free material, from exploits to data dumps. This is a popular dark web site that peddles software exploits which hackers can use to break into your computer or network.

Safe Darknet Market Access Methods
This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself. Apart from the dark web markets that are operating online today, some raided platforms influenced many markets. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. Believe it or not, some dark web marketplaces have pretty advanced systems for building trust.
Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol. It assigns a task to the client instead of the server, eliminating server-related vulnerability. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction. This makes it extremely difficult to find out who you are transacting with.
These features help establish trust between buyers and sellers, providing users with a sense of security that many other markets lack. Silk Road quickly grew into the largest darknet market, handling hundreds of millions in transactions. But in 2013, law enforcement traced Bitcoin activity, monitored DPR’s forum posts, and exploited server vulnerabilities to identify Ross Ulbricht.
How Does The Darknet CC Market Work?
One of the central76 discussion forums was Reddit’s /r/DarkNetMarkets/,777879 which has been the subject of legal investigation, as well as the Tor-based discussion forum, The Hub. Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP. It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products. Established in 2022, Torzon market is one of the biggest and most diverse marketplaces on the dark web.

How To Access The Dark Web
This makes it even harder for third parties to see your email traffic. Awazon became the successor of the popular AlphaBay market, which the authorities shut down successfully in July 2023. Like any other site of such nature, Awazon Market isn’t free from risks, so be careful while accessing it. It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web.
You only need to upload your PGP key or let the platform create one. Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook. This .onion link makes it impossible for hackers to impersonate your profile. Formerly known as Archive.is, it is one of the best onion sites on the dark web. It aims to preserve the internet’s scientific and cultural heritage.