Hidden Answers is one of the biggest question-and-answer dark web sites. This makes Riseup a vital tool for people in oppressive environments or anyone concerned with online privacy. ProPublica is a non-profit investigative journalism outfit based out of New York City. It’s committed to transparency and public service, which is why it maintains a dark website along with its site on the surface web. However, Ahmia doesn’t have a large developer supporting it, so it’s been the target of scams or cyberattacks in the past. Not to be confused with the riskier Hidden Wiki page, Wikipedia on Tor serves as a vast repository of information.
Start Your Protection,
This includes buying or selling illicit goods, illegal transactions, and downloading copyrighted material. ProtonMail is a Swiss-based encrypted email service that doesn’t require personal information when you sign up. ProtonMail’s end-to-end encryption makes it one of the best onion sites for easy-to-use, secure, anonymous email.
Is It Illegal To Enter The Dark Web?
Knowing this, we tested many dark websites, and only the safest and most reliable ones made it to our list of 29 best dark web sites you should know in 2025. Having trouble deciding what dark web sites are safe and reliable? Dark web can be perceived as the world wide web for darknet networks such as Tor, F2F, and others.

However, this does not provide any extra security for your device or information. You won’t be able to search the dark web with a regular browser (such as Chrome or Firefox). Besides, your online activity on such browsers is visible to your ISP unless you connect to a VPN service.
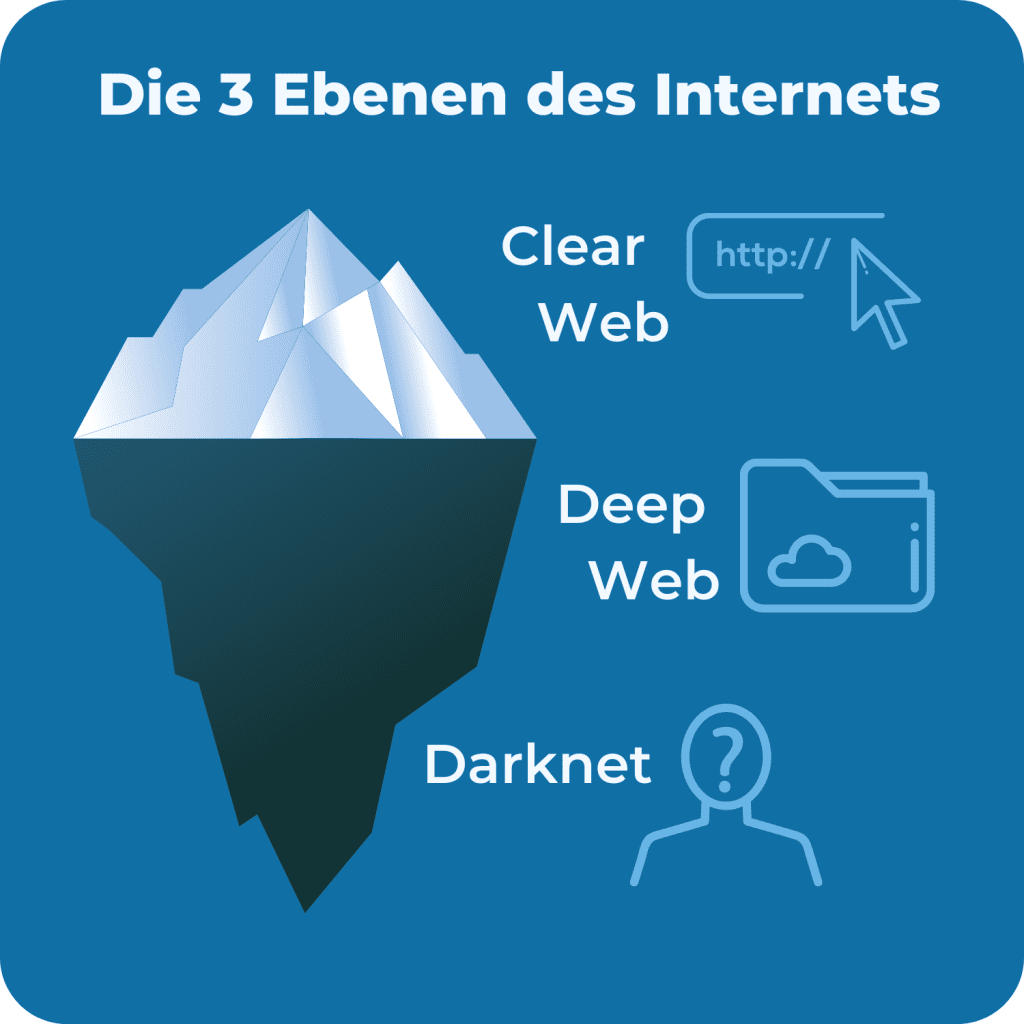
While the deep web comprises about 90% of the total web, the dark web makes up just a tiny fraction of the deep web total. Unless you know where you’re going, there’s always some risk connected to clicking on dark web search engine links. A VPN like Surfshark encrypts your internet connection and makes it harder for others to see your real IP address. This adds another, more reliable security layer to all of your online activity. Many dark web links could get you mixed up in some kind of criminal activity of another, whether you’re looking for it or not.
Deep Web Search Engines (Onion Links
For example, the BBC website is not accessible in such countries. This is where an Onion website, like the Tor browser, comes in handy. With the right precautions and tools like Forest VPN, you can navigate its depths safely and securely. Whether you’re seeking information or privacy, the dark web offers resources that are inaccessible on the surface web. Explore tools and tips for navigating this hidden part of the internet while staying secure.
SecureDrop — Secure File Sharing For NGOs, Journalists & News Organizations
- You can archive any site you want, or retrieve historical records wherever available.
- A preferable choice always would be to buy a paid version of a VPN, but there are freely available VPN services as well.
- Monitoring dark web markets is crucial, no matter if you are a business or individual, as you can then proactively identify and mitigate potential breaches and cyber threats.
- Bear in mind that downloading materials from this site may put you in violation of local copyright laws, so exercise caution should you decide to do so.
Everything you do is protected by NordVPN, which is key to accessing the dark web and enjoying it privately. You need a special browser (Tor) and all of these websites are intentionally obscured. So, to clarify again, this tutorial will cover how to access the dark web privately and safely – not the deep web.
How To Safely Access The Best Dark Web Sites – Quick Guide
Some alternative links are available, providing access to the marketplace. It’s recommended not to use new alternative links as they could just be planned exit scams. Its intuitive interface and advanced search features make it easy to find local and global products. It stands as a reliable alternative to the defunct Alphabay Market as it continues to position itself as the premier source for advanced privacy-focused digital commerce.
Install And Update Security Software
Another great source to find and explore dark web marketplaces or other sections is to visit Reddit’s resourceful forum. You can look for information on /r/deepweb, /r/TOR, or /r/onions, of which the latter is useful to find hidden wikis and more. Many of these Reddits have rules prohibiting linking to illegal sites and services, so you likely won’t find anything illegal there.
It issued a press release revealing that, from December 2021, the website will no longer be functional. The readers like you support Beencrypted to help keep up the good work. When you purchase using links on our website, we may earn an affiliate commission at no extra cost to you. With Tor Browser, you are free to access sites your home network may have blocked. We’re back with another video in our Webz Insider video series on everything web data.
The Legality Of Accessing The Dark Web
After connecting to the VPN, open the Tor browser to access onion sites. Additionally, avoid clicking on suspicious links and downloading files from untrusted sources. While many onion sites may host illegal activities, there are also legitimate sites that provide valuable services, such as secure email and access to information. It’s essential to exercise caution and common sense while browsing. Google only indexes websites on the open web (freely accessible and public), while dark web sites use .onion domains that are not visible to traditional search engines. Awazon Marketplace is the leading dark-web marketplace that claims to provide a secure destination for anonymous trading.
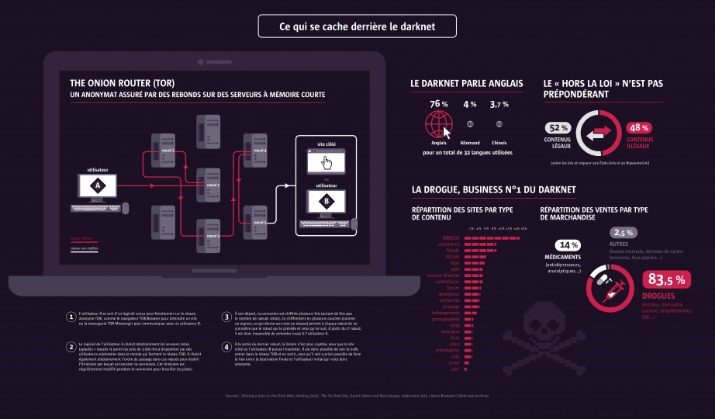
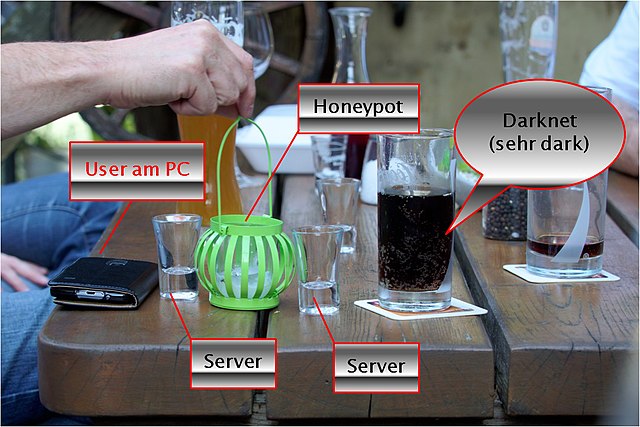
The connection is encrypted, and all the traffic bounces between relays worldwide, making the user anonymous. Journalists and whistleblowers, including Edward Snowden himself, often use the dark web and Tor to exchange sensitive information. For instance, the Ashley Madison data dump was posted to a site only accessible to Tor users. The node requests the data from this server and forwards it to the user. This means that it is not possible to find out where the server is actually located using conventional means. Due to this cascading, the use of file sharing services such as Bittorrent via the Tor network also makes no sense.
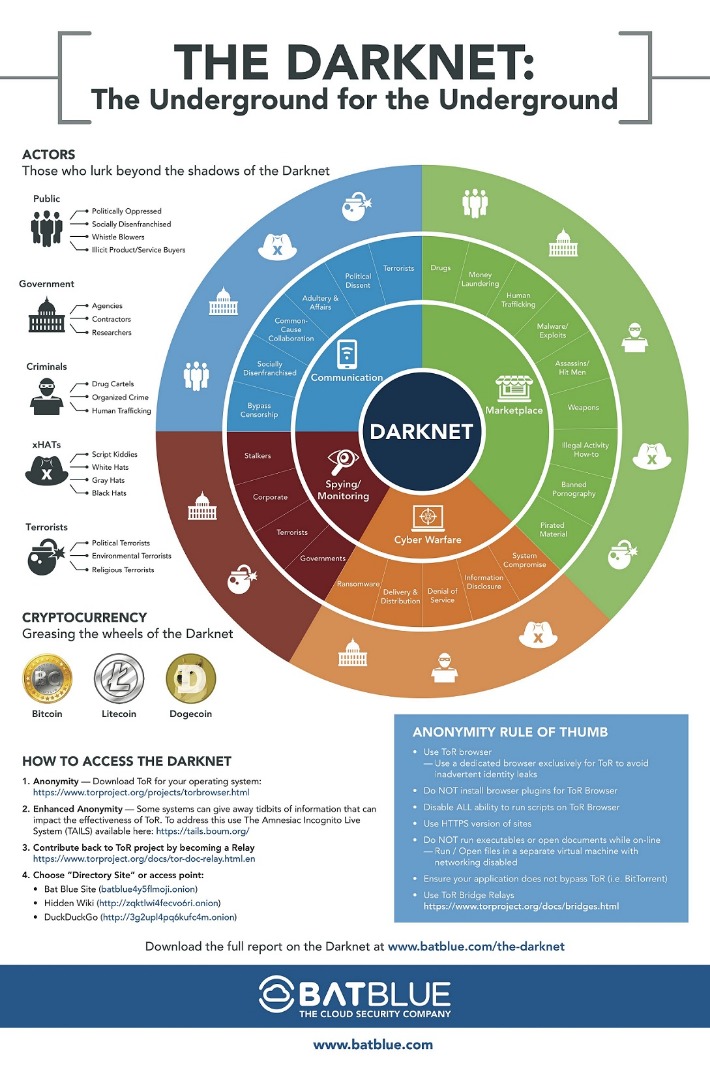
The dark web is the part of the internet that’s not indexed by public search engines like Google. It’s made up of forums, marketplaces, and websites you can’t find with a Google search and requires specialized software to access, such as the Tor Browser. Special software is required to enter this network like the Tor browser, which is required to enter into Tor’s network. TOR can access regular websites also, a website on this network has .onion address. Friend-to-Friend is another kind of darknet where two-person transfer data between them anonymously.
Additionally, much of the materials on the dark web are illegal, and unknowingly downloading such content can implicate you in criminal activities punishable by laws. If your device is infected with malware, read our guide to remove malware from your computer. While Tor lets you reach .onion sites, many require invitations, passwords, or verification. The dark web also offers access to blocked resources in countries with strict government censorship on the internet.
While adoption is early, the shift signals a long‑term move toward censorship‑resistant infrastructure. Market admins use AI to detect scams, fake reviews and phishing links, while law enforcement deploys machine learning to map vendor reputations and analyze seizure data. In parallel, threat actors have begun using LLMs to auto‑generate malware listings and evade keyword filters, accelerating both growth and complexity. Accessing the dark web with tools such as Tor is lawful in most democracies, but what you do there is governed by criminal, consumer‑protection and anti‑money‑laundering statutes. In every jurisdiction, buying or selling contraband—drugs, malware, counterfeit IDs—remains illegal, and penalties can be severe. Operational security, or OPSEC, is the discipline that turns technical anonymity into real‑world protection.