Some P2P enable off-ramping via cash and prepaid vouchers, bypassing AML compliance under claims of mere facilitation. Regulatory countermeasures, including blockchain analytics and the FATF’s Travel Rule, aim to trace illicit flows. However, enforcement inconsistencies highlight the ongoing struggle between financial privacy and regulatory oversight in combating cryptocurrency-enabled money laundering. Cryptocurrency money laundering methods have dominated the development of blockchain technology, using privacy tools and decentralized infrastructure to conceal illicit financial transactions. The methods take advantage of the pseudonymous nature of cryptocurrencies and evolve constantly to remain one step ahead of regulatory monitoring and blockchain analytics. Cryptocurrencies have revolutionized the global finance environment with financial inclusion, efficiency, and decentralization capabilities.

Investigating The Staged Assassinations Of Silk Road
Global cooperation, adaptive legal frameworks, and cross-border enforcement are crucial in addressing emerging threats. By harmonizing regulation, security, and technological advancements, the cryptocurrency ecosystem can become more transparent, secure, and sustainable, fostering trust and long-term growth in digital financial markets. Cryptocurrencies allow extremist organizations to bypass conventional financial limitations, leveraging pseudonymity to mobilize foreign funds. Terror groups usually use bitcoin and privacy coins to mobilize funds, capitalizing on regulatory loopholes.
We showed that a small fraction of traders is responsible for a large fraction of the trading volume, and by analysing the networks of buyers and sellers, we found different resilience regimes. Shocks tend to induce serious structural changes in the multiseller network, but impact the multibuyer network much less severely. Interestingly, the S2S network shows an intermediate level of resilience, which suggests that the S2S network might play the role of a supply chain network on the dark web. Furthermore, after a shock, the activity of buyers is resumed almost immediately, while the activity of sellers recovers more slowly.
Cyble Titan Endpoint Security
We find that half of the DWM users trade through U2U pairs generating a total trading volume greater than DWMs themselves. We then show that hundreds of thousands of DWM users form stable trading pairs that are persistent over time. Users in such stable pairs turn out to be the ones with the largest trading volume on DWMs. Then, we show that new U2U pairs often form while both users are active on the same DWM, suggesting the marketplace may serve as a catalyst for new direct trading relationships.
- You’ll get stolen credit cards, remote desktop account info, personal details, and various logs.
- These lists are curated based on user feedback, uptime, and overall reputation, making them indispensable tools for navigating the darknet landscape.
- Moreover, we observe a trend of increase in their median income relative to the value before operation Bayonet—an increase of almost six times by the end of the period of observation (see Supplementary Information S4).
- Interestingly, the S2S network shows an intermediate level of resilience, which suggests that the S2S network might play the role of a supply chain network on the dark web.
Features like multi-signature wallets, end-to-end encrypted messaging, and decentralized hosting environments reduce the risk of detection. Many vendors rotate addresses and aliases regularly to avoid tracking and maintain anonymity. Abacus Market, the largest Western darknet marketplace supporting Bitcoin payments, has shut down its public infrastructure in a move suspected to be an exit scam. In early July, Abacus Market, the largest Bitcoin‑based Western darknet marketplace, abruptly went offline, triggering widespread suspicions of an exit scam. As the darknet continues to grow, its markets are expected to adopt even more sophisticated tools for secure trading, further enhancing the user experience and solidifying their role in modern commerce.
How To Access Verified Dark Web Sites
The second category consists of data stores, which specialize in stolen information. In 2023, the dark web attracted an average of 2.7 million daily users, with Germany now leading as the country with the highest number of Tor users, surpassing the United States for the first time in years. Additionally, Dread forum administrators – who have close ties to Abacus – have cast doubt on the law enforcement theory. After dominating the ecosystem with over 70% market share and recording $6.3 million in monthly sales, its sudden disappearance has shocked the community. This was reflected in the sharp decline in deposit volumes to Abacus between June and July, 2025.
Bitcoin Darknet Marketplace Abacus Market Goes Dark, Exit Scam Suspected
This ensures that transactions remain untraceable, providing a layer of security unmatched by traditional online platforms. Additionally, many markets now integrate PGP encryption for communication, further safeguarding sensitive information. Additionally, the integration of Bitcoin and other cryptocurrencies has streamlined transactions, eliminating the need for traditional banking systems. This not only enhances privacy but also reduces the risk of financial tracking.
How KELA Cyber Supports You In Darknet Monitoring And Risk Mitigation

Darknet markets provide a secure platform for trading various goods, including pharmaceuticals and digital products. These platforms, accessible via darknet links and onion addresses, ensure anonymity through encryption and cryptocurrency transactions. The best darknet markets in 2025 offer user-friendly interfaces, reliable vendor ratings, and diverse product listings. Darknet market lists and darkmarket URLs help users navigate the ecosystem efficiently.
Emergence And Structure Of Decentralised Trade Networks Around Dark Web Marketplaces
It uses PGP encryption to protect sensitive data and messages, and accepts payments via Monera and Bitcoin to keep you anonymous on this marketplace. Another dark net marketplace that has grabbed a lot of attention is the Hydra market. It accepts payments through Bitcoin and the Escrow system and ensures that your identity remains anonymous during your purchases. During our tests for the research, we were able to register with a bogus email and a random username.
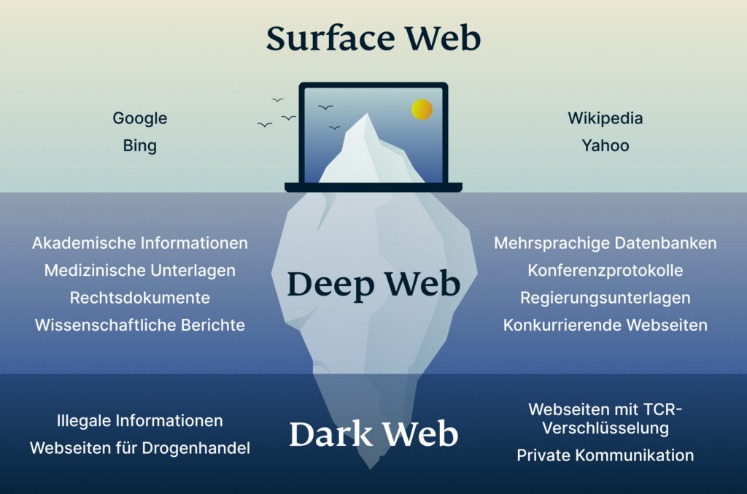
TRM Labs estimates that total transactions, including Monero, may have reached $300–$400 million. The disappearance appears to be a move for self-preservation, as law enforcement attention increased after Archetyp’s seizure. TRM Labs reports that both its clearnet mirror and hidden-service infrastructure became inaccessible, and the site’s operator, known only as “Vito,” vanished along with users’ escrowed funds. The immutable ledger in the Bitcoin blockchain had considerably aided law enforcement to track the illegal transactions of Silk Road. To access sites in the Darknet, users need to use special software such as the Tor Browser as they are on an encrypted network to hide the identities of the people running the sites and services connected to them. For those prioritizing variety, EclipseMarket stands out with its extensive catalog of pharmaceuticals, recreational drugs, and rare substances.
Besides, not everyone wants to purchase an illegal item – some want items anonymously. Who doesn’t like privacy, especially when dealing with the buying and selling of illegal products and services? Therefore, given the nature of anonymity and privacy of the dark web, several stores keep on emerging in the dark despite a continuous crackdown on several others. We understand the curiosity to venture into the dark web, but you also need to understand that it’s never safe to venture into this portion of the internet without fully understanding what it entails. Discover everything about what is a darknet market, how it works, security threats related to it, and learn how to protect your data online.
- The popular Silk Road was the first dark web marketplace that you could only access via the Tor Browser.
- CBD oil is a popular pain relief remedy that can alleviate a range of afflictions.
- In 2022 Abacus held 10 percent of Bitcoin sales among Western darknet markets, rising to 17 percent in 2023.
- To be classified as a seller, an entity must simultaneously satisfy the six feature threshold criteria, as follows.
The unique part is that the platform offers free samples of stolen information, often to attract more customers. In this era, it takes one wrong click and all your sensitive data ends up in the wrong hands. Therefore, you need to take your privacy seriously and start by using strong and unique passwords for every online account you open. Unfortunately, the platform was shut down in 2013 after an extensive investigation that was spearheaded by US Senator Charles Schumer. The dark web is not a place that you can venture into without protection and caution; a slight slip-up can lead to major consequences.
Users interacting with other users form U2U pairs and we include them in our dataset. We discard single Bitcoin transactions below $0.01 or above $100,000, which are unlikely to show real purchases and minimise false positives. They may be attributed to a residual amount of Bitcoins in an address or transactions between two business partners where no good is actually given in return, respectively. The analysed dataset includes about 31 million transactions among more than 16 million users. By definition, users that interact among themselves form U2U transactions. If the pair of users interact with multiple DWMs these U2U transactions are included in all related DWMs and counted multiple times.
Explore Content
Efficient navigation is facilitated by darknet market lists and onion URLs, which are regularly updated to ensure accessibility. These lists often include filters for categories, prices, and vendor reputation, streamlining the search process. Bitcoin remains the primary currency, offering anonymity and ease of use, though some markets are beginning to integrate alternative cryptocurrencies for added flexibility. The starting point for this paper is the identification of U2U networks around DWMs. We analyse 40 DWMs for the time period spanning from June 18, 2011 to January 31, 2021. Our dataset covers all major DWMs that have ever existed, as identified by the European Monitoring Centre, Europol, the World Health Organization, and independent researchers24,25,26.